MDM for Remote and Hybrid Teams — Managing Devices Beyond the Office
Mobile Device Management (MDM) was built for devices that leave the building. Phones travel. Laptops connect to home Wi-Fi, hotel networks, and airport terminals. Tablets operate in vehicles, clinics, and warehouses with unreliable cellular coverage. MDM manages every one of these devices regardless of network, location, or time zone — enforcing security policies, pushing app updates, and giving IT remote visibility without requiring devices to check in at the office.
For remote and hybrid teams, MDM is not optional infrastructure. It is the only mechanism IT has for enforcing encryption on a laptop connected to a personal hotspot in another country, revoking corporate app access on a phone that a departed employee still carries, or patching an OS vulnerability on 500 devices scattered across 30 cities. Solutions like Bento MDM deliver all of these capabilities at $1/device — the same console and license that manage office devices also manage remote ones.
This guide covers how MDM enforces policies on remote devices, how it handles BYOD for distributed teams, how IT troubleshoots devices without site visits, and how onboarding and offboarding work when employees never enter the office. For the foundational definition of MDM — what it is, how it works, and what it manages — start with what mobile device management is and how it works.
What Is Remote Device Management?
Remote device management is MDM applied to devices that operate outside the corporate network. The MDM agent installed on each device communicates with the MDM server over the internet (HTTPS) — not over a VPN or the corporate LAN. Policies, app updates, security commands, and compliance checks travel between the server and the device on any available connection: home Wi-Fi, cellular, public hotspot, or satellite.
This is a critical distinction. MDM follows the device, not the network. A security policy that enforces full-disk encryption, blocks USB file transfers, and requires a 6-digit PIN applies whether the device is on the office LAN or on a coffee shop network in another country. The device does not need to “come back to the office” to receive its next policy update.
Remote device management is not the same as remote access tools like TeamViewer or AnyDesk. Those tools provide screen sharing for troubleshooting. MDM manages the entire device lifecycle — enrollment, policy enforcement, app distribution, compliance monitoring, and remote wipe. MDM includes remote view and control as one of many capabilities. For the full breakdown of where MDM ends and remote monitoring tools begin, see MDM vs RMM — when you need device management vs remote monitoring.
How MDM Enforces Policies on Remote Devices
MDM policy enforcement does not depend on the corporate network. Three mechanisms make this work: cloud-based policy delivery, VPN auto-connect for corporate resource access, and zero-trust posture checks that verify device health before granting access to anything.
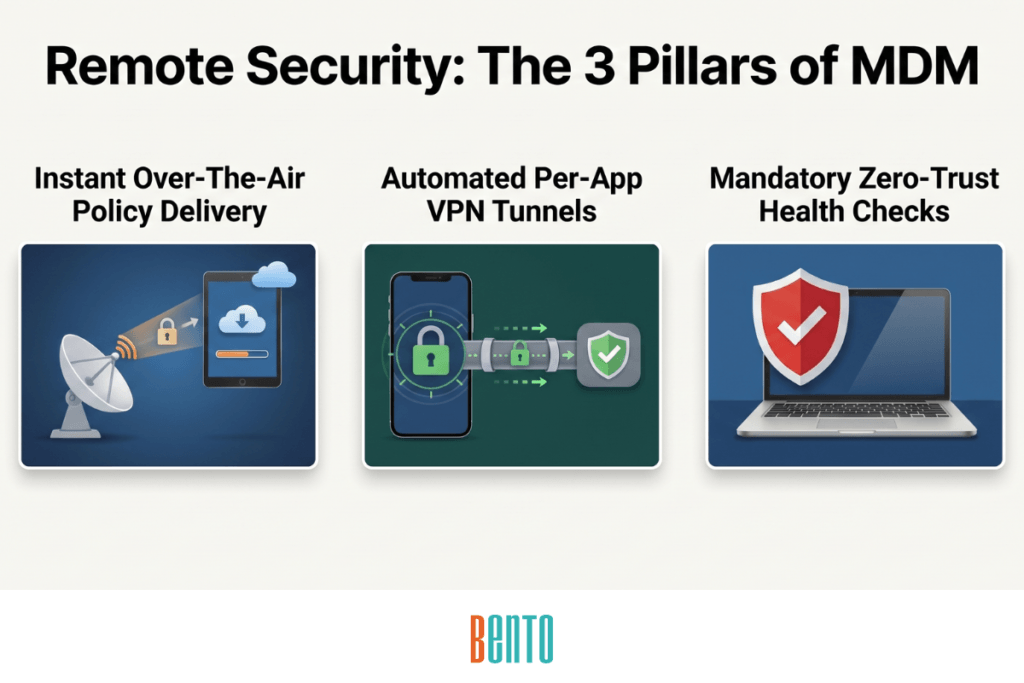
Cloud-Based Policy Delivery
The MDM agent on each device checks in with the MDM server on a configurable schedule—or on connectivity events (new Wi-Fi, SIM change, reboot). When the server has a new or updated policy, it pushes the payload over the air. The device applies the policy immediately. No VPN tunnel, no corporate network proximity, no user action required. This is the same over-the-air mechanism described in how MDM deployment and enrollment work, extended to every network the device connects to.
VPN Auto-Connect and Per-App VPN
MDM pushes VPN profiles to managed devices that activate automatically when the device connects to any untrusted network. Always-on VPN routes all traffic through the corporate tunnel. Per-app VPN routes only corporate app traffic — the EHR app, the CRM, the intranet browser — through the tunnel, while personal browsing goes direct. Split tunneling reduces bandwidth load on the corporate VPN concentrator without sacrificing security for managed applications.
Per-app VPN is particularly important for BYOD on remote teams. Employees do not want all of their personal traffic flowing through the company VPN. Per-app VPNs isolate corporate traffic without affecting personal browsing, streaming, or messaging. This separation is central to the BYOD vs COPE vs CYOD ownership model decision that every remote-first organization must make.
Zero-Trust Posture Checks
Before a remote device accesses corporate resources — email, file shares, SaaS applications — MDM verifies that the device meets the organization’s security baseline. The posture check evaluates whether encryption is enabled, the OS version is current, no root or jailbreak is detected, the password policy is met, the MDM agent is active, and the device is enrolled in good standing. If any check fails, the device is quarantined from corporate resources until remediated.
This is zero-trust applied at the device level. The network the device connects to is irrelevant — the device itself must prove its posture before access is granted. For a deeper treatment of MDM’s role in endpoint security and zero-trust architecture, see how MDM protects enterprise data.
BYOD for Remote and Hybrid Workers
Remote teams run on personal devices. An employee hired in a city where the company has no office uses their own laptop and phone from day one. BYOD is not a policy choice for fully remote organizations — it is the default. MDM makes it manageable.
Work Profile Containerization on Android
Android Work Profile creates a separate, encrypted container on the employee’s personal device for corporate apps, email, and data. IT manages the Work Profile independently — pushing apps via managed Google Play, enforcing password policies, configuring per-app VPN, and restricting copy-paste between corporate and personal apps. The employee’s personal photos, messages, and apps remain private and untouched. On offboarding, IT selectively wipes only the Work Profile without affecting personal data.
Managed App Configuration on iOS
On iOS, MDM achieves BYOD separation through managed app configurations and managed open-in restrictions. Corporate apps installed by MDM receive per-app VPN profiles, server URLs, and license keys pushed silently. Managed open-in prevents corporate documents from being shared to personal apps (and vice versa). Safari can be configured with URL filters that apply only to managed browsing sessions. Personal apps remain private — IT cannot see, read, or control them.
What MDM Can and Cannot See on BYOD Devices
This is the most common concern remote employees raise — and the most common reason they resist MDM enrollment. The answer is concrete:
| Data Category | BYOD — Android Work Profile | BYOD — iOS Managed Apps | Fully Managed (Corporate-Owned) |
|---|---|---|---|
| Device model & serial number | ✓ Visible | ✓ Visible | ✓ Visible |
| OS version & security patch level | ✓ Visible | ✓ Visible | ✓ Visible |
| Encryption status | ✓ Visible | ✓ Visible | ✓ Visible |
| Managed (corporate) apps installed | ✓ Work Profile apps only | ✓ Managed apps only | ✓ All installed apps |
| Personal apps installed | ✗ Not visible | ✗ Not visible | ✓ Visible (IT owns the device) |
| Corporate browsing history | ✓ Managed browser in Work Profile | ✓ Managed browser only | ✓ All browsing (if content filtering enabled) |
| Personal browsing history | ✗ Not visible — outside Work Profile | ✗ Not visible — personal Safari untouched | ✓ Visible (IT owns the device) |
| Personal photos & videos | ✗ Not visible — OS enforced | ✗ Not visible | ✗ Not visible (MDM does not access media files) |
| Text messages & call history | ✗ Not visible | ✗ Not visible | ✗ Not visible (MDM does not access message content) |
| Personal email content | ✗ Not visible | ✗ Not visible | ✗ Not visible (MDM does not read email) |
| GPS location | ✗ Not tracked unless IT enables & user consents | ✗ Not tracked unless IT enables & user consents | ✓ Trackable (IT owns the device) |
| Compliance status (policy met/not met) | ✓ Work Profile compliance only | ✓ Managed app compliance only | ✓ Full device compliance |
| Wi-Fi network name | ✗ Not visible | ✗ Not visible | ✓ Visible |
| Remote wipe scope | Work Profile only — personal data untouched | Managed apps & configs only — personal data untouched | Full device factory reset |
| Camera & hardware restrictions | ✗ Cannot restrict personal-side hardware | ✗ Cannot restrict personal-side hardware | ✓ Can disable camera, USB, Bluetooth, screenshots |
On Android Work Profile devices, IT literally cannot access anything outside the Work Profile container. The separation is enforced by the operating system, not by the MDM vendor. For a full breakdown of how BYOD, COPE, and CYOD ownership models affect what IT can and cannot control, see BYOD vs COPE vs CYOD — which ownership model fits your organization.
A written BYOD policy should document exactly what MDM can and cannot see, and every employee should acknowledge it before enrollment. For a template, see the MDM policy template with BYOD sections.
Remote Troubleshooting Without Site Visits
When a remote employee’s device fails, IT cannot walk to their desk. The device is in their apartment, their car, or a co-working space in a different time zone. MDM provides three mechanisms for resolving issues without dispatching anyone.
Remote View and Control
MDM remote view streams the device’s screen to the IT admin’s console in real time. The admin sees exactly what the employee sees — the error message, the misconfigured setting, the frozen app. Remote control lets IT interact with the device directly: tapping, swiping, navigating menus, and modifying settings as if holding it. On fully managed (Device Owner) Android devices, this works without user interaction — no acceptance prompt needed. On BYOD devices, the employee approves the session via an on-screen prompt.
Remote Shell and Log Collection
Not every issue requires a screen-sharing session. MDM remote shell lets IT execute commands on the device — checking connectivity (ping, traceroute), verifying app versions, clearing app caches, collecting crash logs, and restarting services. Log collection retrieves diagnostic data from the device and uploads it to the admin console for analysis. These actions happen in seconds and do not require the employee to be present or aware.
Just-in-Time Remote Access
For contractors, third-party support, or temporary IT staff who should not have standing remote access to managed devices, MDM provides just-in-time (JIT) remote sessions. The admin grants a time-limited remote access window that auto-expires at the end of the session — 15 minutes, 1 hour, or a custom duration. No persistent credentials. No standing access. This is critical for remote teams that use external IT support providers. Bento MDM’s just-in-time remote access enforces automatic expiration and logs every session for audit.
Patching and Compliance for Distributed Fleets
Remote devices miss patch windows. A laptop that is not connected to the corporate network does not receive the SCCM update. A phone on cellular in a different time zone reboots at midnight local time, not during the IT-scheduled maintenance window. MDM solves this because patching happens over the air, on the device’s schedule, via the MDM agent—not through network-dependent tools.
Over-the-Air Patch Deployment
MDM pushes OS updates and app patches to every managed device over the internet. Updates can be scheduled during off-hours relative to the device’s local time zone, staged by device group (pilot group first, then wider rollout), and configured to install automatically or with a deferral window that the employee controls. The device downloads the update on its next connectivity event and applies it during the configured window. For the complete patching workflow, including rollback procedures and compliance reporting, see MDM best practices for device fleet management.
Continuous Compliance Monitoring
MDM compliance dashboards show which remote devices are compliant and which are not — in real time. Compliance metrics include OS version (is it patched?), encryption status (is it enabled?), password policy (does it meet minimum requirements?), root/jailbreak detection (is the device compromised?), and MDM agent health (is it reporting?). Non-compliant devices trigger automatic alerts. IT can configure escalation actions, such as warning the user, restricting access to corporate resources, or quarantining the device from the fleet.
Compliance monitoring becomes more important as the fleet becomes more distributed. When all devices are in one building, IT can spot-check physically. When devices are in 30 countries, the compliance dashboard is the only source of truth. The MDM capabilities checklist covers compliance monitoring as one of the 12 core capabilities every MDM solution must have.
Offline Policy Enforcement
Remote devices in locations with unreliable connectivity — such as construction sites, rural clinics, mining operations, and maritime vessels — may not always be able to reach the MDM server for their next check-in. Bento MDM’s Offline QR Commands solve this: a supervisor scans a QR code generated in the admin console, and the encrypted policy payload is transferred to the device via the camera, with no internet connection required. The device applies the policy, confirms the change, and syncs with the server on its next connectivity event. No other MDM solution offers this capability.
Onboarding and Offboarding Remote Employees
The two most critical MDM workflows for remote teams are getting a new hire productive on day one and revoking all corporate access on the last day — both without physical proximity.
Zero-Touch Onboarding
The company ships a device to the remote employee’s home address. The employee opens the box, powers on the device, and connects to any Wi-Fi network. The device contacts the MDM server automatically via zero-touch enrollment (Android), Apple Automated Device Enrollment (iOS/macOS), or Windows Autopilot. The MDM agent downloads, the assigned profile applies, corporate apps install silently, VPN configures, and the device is ready for work. No IT visit. No manual configuration steps. No app store browsing.
For BYOD onboarding, the process is different. IT sends the remote employee an enrollment link or QR code. The employee scans it, approves the MDM profile (which discloses exactly what IT will manage), and the Work Profile or managed apps install alongside their personal setup. The MDM implementation guide covers both corporate-owned and BYOD enrollment workflows in detail.
Selective Wipe on Offboarding
When a remote employee leaves the organization, IT executes a remote wipe from the MDM console. On BYOD devices, this is a selective wipe — only the Work Profile (Android) or managed apps and configurations (iOS) are removed. Personal photos, messages, and apps remain untouched. The former employee keeps their personal device exactly as it was, minus corporate access.
On corporate-owned devices, IT can execute a full factory reset remotely — returning the device to out-of-box state for redistribution to the next hire. Factory reset protection prevents the former employee from reactivating the device without IT authorization, even if they attempt to set it up again.
International and Multi-Timezone Considerations
Fully remote organizations operate across countries, time zones, cellular carriers, and regulatory jurisdictions. MDM must accommodate all of them from one console.
Patch scheduling must respect local time zones. An update scheduled for “2 AM” needs to mean 2 AM in the device’s local time, not 2 AM at headquarters. MDM platforms that schedule by server time push updates at noon for half the fleet and at 3 AM for the other half — disrupting workdays unnecessarily.
Cellular data costs vary dramatically by country. MDM web content filtering reduces unnecessary bandwidth consumption by blocking streaming, social media, and large downloads on cellular-connected devices. APN configuration ensures that devices switching between carriers in different countries connect to the correct network with the right data plan settings.
Regional compliance adds another layer. Employees in the EU are protected by GDPR, which restricts what device data IT can collect and how long it can be retained. Employees accessing patient data in the US require HIPAA-compliant MDM configurations. A global MDM policy must accommodate both simultaneously — typically through device group segmentation, where EU devices receive GDPR-aligned data collection policies and US clinical devices receive HIPAA-aligned encryption and audit policies.
Frequently Asked Questions
Do I need MDM if my team is fully remote?
Yes. Remote teams are the primary use case for MDM today. Without MDM, IT has no mechanism to enforce encryption on a laptop connected to an employee’s home network, push security patches to a phone on a cellular network, revoke corporate access on a departed employee’s device, or verify that 500 distributed devices meet the organization’s security baseline. If devices access corporate data and IT cannot physically touch them, MDM is required.
What is remote device management?
Remote device management is Mobile Device Management (MDM) applied to devices that operate outside the corporate network. The MDM agent on each device communicates with the MDM server over the internet, receiving policies, app updates, and commands regardless of the device’s location or network. Remote device management covers enrollment, security policy enforcement, app distribution, compliance monitoring, remote troubleshooting, and remote wipe — all performed over the air.
Can my employer see my personal data with MDM on a BYOD device?
No. On Android devices with Work Profiles, the MDM manages only the corporate container. IT can see the device model, OS version, encryption status, and the list of managed corporate apps. IT cannot see personal photos, text messages, browsing history, personal app data, or any content outside the Work Profile. On iOS, MDM manages only the apps and configurations it installed. The operating system enforces the separation.
How does MDM work without a VPN?
MDM does not require a VPN for policy delivery. The MDM agent communicates with the MDM server over HTTPS — the same encrypted protocol used by every website. Policies, app updates, and commands are pushed over the air on any internet connection. VPN is used for corporate resource access (email servers, intranet portals, internal applications), not for MDM management. A device can receive its MDM policies on public Wi-Fi and still be fully managed.
What is the difference between MDM and remote access tools like TeamViewer?
MDM manages the entire device lifecycle — enrollment, policy enforcement, app distribution, security configuration, compliance monitoring, and remote wipe. Remote access tools like TeamViewer, AnyDesk, or Chrome Remote Desktop support screen sharing for troubleshooting, but only in a single session at a time. MDM includes remote view and control as a single capability, but its primary function is managing the device—not just viewing its screen. MDM operates continuously; remote access tools operate on demand.
How do I onboard a remote employee with MDM?
For corporate-owned devices, ship the device to the employee’s address. They connect to Wi-Fi and the device auto-enrolls via zero-touch enrollment (Android), Apple Automated Device Enrollment (iOS/macOS), or Windows Autopilot. Apps install, policies apply, and VPN configures automatically. For BYOD, send the employee an enrollment link or QR code. They scan it, approve the management profile, and install corporate apps alongside their personal setup. Both workflows require zero IT presence at the employee’s location.
Related Articles