MDM Security — How Mobile Device Management Protects Enterprise Data
MDM security is the layer of endpoint protection that enforces encryption, access controls, and compliance policies on every mobile device that accesses corporate data. Mobile Device Management (MDM) does not detect threats or block attacks — that is the job of Mobile Threat Defense (MTD) and Endpoint Detection and Response (EDR) tools. MDM prevents unauthorized access, enforces compliance baselines, and ensures that when a device is lost, stolen, or compromised, corporate data can be remotely erased before it is exposed.
MDM is a prevention layer, not a detection layer. It reduces the attack surface by enforcing the security baseline that makes detection and response tools effective. A device with MDM-enforced encryption, automated patching, and access controls is a harder target than one without — but it is not invulnerable. Understanding what MDM protects and what it does not is the difference between a security strategy that works and one with gaps.
This guide breaks down MDM’s 7 security control layers, explains where MDM fits in a zero-trust architecture, and honestly addresses what MDM cannot protect against.
The 7 Security Controls MDM Enforces
MDM security operates at the device and policy layer. It controls how devices are configured, what they can access, and how they respond to security events. These 7 controls represent the complete MDM security stack — from data-at-rest protection through offline enforcement.
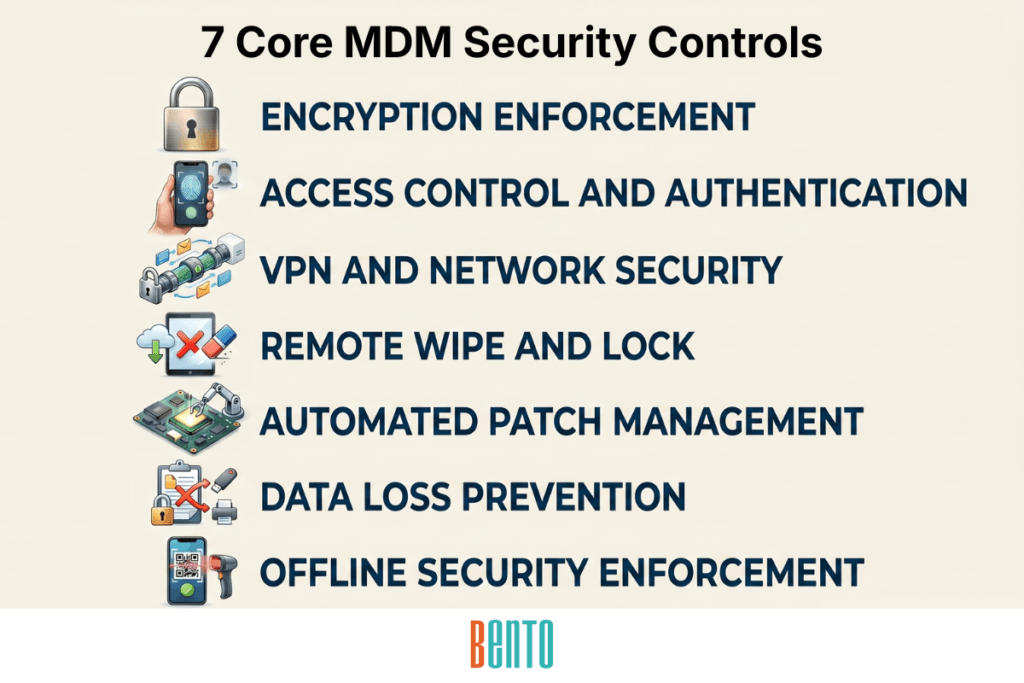
1. Encryption Enforcement
MDM enforces full-disk encryption on every enrolled device, so data at rest is protected even if the device is physically stolen. MDM continuously verifies encryption status — a device that reports encryption disabled is flagged as non-compliant and automatically quarantined until encryption is re-enabled. On Android, MDM enforces AES-256 encryption. On macOS, it manages FileVault. On iOS, hardware-level encryption is always active, but MDM verifies that it is not circumvented by jailbreaking.
Encryption enforcement is non-negotiable for any device that stores corporate data, credentials, or regulated information. Without it, a stolen laptop is an open file cabinet.
2. Access Control and Authentication
MDM enforces passcode complexity requirements (minimum length, alphanumeric, no sequential patterns), biometric authentication (fingerprint, face recognition), lockout thresholds (device locks after X failed attempts), and session timeouts (auto-lock after inactivity). Multi-factor authentication can be required for device unlock, app access, or admin console login.
Role-based access control (RBAC) restricts which administrators can perform which management actions. A device admin can enroll endpoints, but cannot trigger a remote wipe. An auditor can view compliance reports but cannot change policies. Every admin action is logged in the audit trail against a named user.
MDM integrates with identity providers — Active Directory, LDAP, SAML, and OAuth — for centralized authentication. When an employee is deprovisioned from the directory, their device access is revoked automatically. No manual MDM cleanup required.
3. VPN and Network Security
MDM pushes VPN profiles that encrypt all corporate traffic in transit. Per-app VPN routes only corporate application traffic through the encrypted tunnel — personal browsing, streaming, and messaging stay on the regular network. Always-on VPN prevents corporate data from being transmitted unencrypted, even if the user manually disconnects.
MDM also pushes Wi-Fi profiles with certificate-based authentication. Devices connect to trusted corporate networks automatically without users entering credentials or selecting the wrong SSID. On untrusted networks (hotel Wi-Fi, airport hotspots, coffee shops), the VPN activates automatically to protect corporate traffic.
4. Remote Wipe and Lock
MDM enables IT to remotely lock or wipe a device the moment it is reported lost, stolen, or compromised. Two wipe modes exist: selective wipe removes only corporate data and the work profile, leaving personal content untouched (standard for BYOD). Full wipe performs a factory reset that erases everything on the device (standard for corporate-owned devices).
Factory reset protection (FRP) prevents a wiped device from being reactivated without the required credentials. A stolen phone that gets factory-reset becomes a brick — the thief cannot set it up as a fresh device because FRP requires the original MDM enrollment credentials to proceed. Without FRP, a remote wipe protects the data but gives the thief a working phone. With FRP, both the data and the hardware are secured.
5. Automated Patch Management
MDM automatically pushes OS and application updates on a schedule set by IT. Unpatched devices are the most exploited attack surface in enterprise mobile security — known vulnerabilities in outdated operating systems and applications are the entry point for the majority of mobile compromises.
MDM removes the user from the patching equation. Updates deploy automatically during maintenance windows. Enforcement deadlines force installation within a defined period. Rollback capability reverts updates that cause compatibility issues. Patch compliance dashboards show which devices are up to date and which are behind, with automated alerts when a device misses an update deadline.
6. Data Loss Prevention and Content Controls
MDM restricts how data moves between corporate and personal applications. Copy-paste restrictions prevent users from copying sensitive data (patient records, financial information, customer PII) from corporate apps into personal messaging or cloud storage. Open-in restrictions prevent corporate documents from being shared through unapproved channels. Screen capture disables screenshots and screen recordings of sensitive app content. Content filtering blocks access to malicious websites, phishing domains, and non-productive URLs across the managed fleet.
These controls operate at the device policy layer—they are continuously enforced by the operating system, not by individual applications. A user cannot circumvent copy-paste restrictions by switching apps or using third-party tools, because the restriction is enforced at the OS level by the MDM profile.
7. Offline Security Enforcement
Standard MDM security controls depend on connectivity — if the device cannot reach the MDM server, new policies cannot be pushed, compliance cannot be verified in real time, and management commands cannot be delivered. This creates a security gap for devices operating in disconnected environments, such as mines, ships, aircraft, disaster recovery zones, rural field service locations, and air-gapped government facilities.
Bento MDM’s Offline QR Commands close this gap. IT generates a QR code containing a policy update or management command in the admin console. The field worker scans the QR code with the device camera. The command executes locally — no network connection required. Policies are enforced offline. Security configurations update offline. Troubleshooting commands execute offline. No other MDM vendor offers this capability, and for organizations with devices in disconnected environments, it extends MDM security enforcement to locations where no other MDM solution can operate.
Where MDM Fits in a Zero-Trust Architecture
Zero trust requires verification of every device, user, and network connection before granting access to corporate resources. No device is trusted by default — not even one inside the corporate firewall. MDM provides the device verification layer in this architecture.
Before a mobile device accesses corporate email, a VPN-protected network, or a cloud application, MDM performs posture checks: Is the device enrolled in the MDM platform? Is full-disk encryption active? Is the operating system running a supported version? Is the device jailbroken or rooted? Is the passcode policy compliant? Is the last check-in within the allowed window? A device that fails any posture check is blocked from accessing corporate resources until remediated.
MDM does not replace the other layers of a zero-trust stack. Identity and Access Management (IAM) verifies the identity of the user requesting access. MDM verifies the device — is the requesting endpoint secure? Zero Trust Network Access (ZTNA) verifies whether a network connection is trusted. Mobile Threat Defense (MTD) and EDR detect active threats — is the device currently under attack? All four layers must be present. MDM’s specific contribution is posture enforcement: ensuring the device meets the security baseline before anything else in the stack evaluates the request.
Bento MDM provides security monitoring through a device posture verification layer that checks enrollment status, encryption, OS version, jailbreak status, and passcode compliance before granting access to corporate resources. For organizations building zero-trust architectures, MDM is the foundation on which all other layers depend.
What MDM Cannot Protect Against
MDM is a prevention and enforcement tool. It reduces attack surface and enforces compliance baselines. It does not detect active threats, inspect network traffic, or analyze user behavior. Naming these limitations is not a weakness — it is an accurate description of MDM’s scope that determines what other tools must accompany it.
Malware and zero-day exploits. MDM does not scan files, analyze app behavior, or detect malicious code executing on a device. Mobile Threat Defense (MTD) tools — Zimperium, Lookout, Wandera — handle threat detection on mobile endpoints. MDM and MTD are complementary: MDM enforces the security baseline, MTD detects threats that evade it.
Network attacks. MDM pushes VPN profiles and Wi-Fi configurations, but it does not inspect network traffic for man-in-the-middle attacks, DNS hijacking, or SSL stripping. Zero Trust Network Access (ZTNA) and Secure Access Service Edge (SASE) tools handle network-layer security.
Behavioral analytics. MDM does not analyze user behavior for insider threats, anomalous access patterns, or credential misuse. User and Entity Behavior Analytics (UEBA) and Security Information and Event Management (SIEM) tools handle behavioral detection.
Application vulnerability scanning. MDM distributes and manages applications but does not scan them for vulnerabilities, malicious SDKs, or embedded tracking. Mobile app vetting and software composition analysis tools handle app-level security assessment.
Novel phishing attacks. MDM’s content filtering can block known malicious URLs and phishing domains from a maintained blocklist. It cannot detect novel phishing campaigns, social engineering attempts, or zero-day phishing URLs that have not yet been categorized.
MDM reduces the attack surface. MTD, EDR, ZTNA, SIEM, and UEBA detect and respond to threats that get through. A security strategy that treats MDM as the only mobile endpoint protection layer has a detection gap. A strategy that runs MDM alongside threat detection tools provides defense-in-depth.
MDM Security vs Endpoint Security vs Mobile Threat Defense
The table below compares MDM security with two adjacent security tool categories — Endpoint Detection and Response (EDR) and Mobile Threat Defense (MTD). Each operates at a different layer. MDM enforces the baseline. EDR detects threats on all endpoints. MTD specifically detects threats on mobile endpoints.
| Attribute | MDM Security Mobile Device Management |
Endpoint Security (EDR) Endpoint Detection and Response |
Mobile Threat Defense (MTD) Mobile-Specific Threat Detection |
|---|---|---|---|
| What it protects | Mobile device configuration, data access, and compliance posture | All endpoints (desktops, servers, some mobile) against active threats and malicious behavior | Mobile devices against malware, phishing, rogue networks, and OS exploits |
| How it works | Enrollment-based policy enforcement — pushes security configs, restrictions, and compliance baselines over the air | Agent-based threat detection — monitors endpoint behavior, files, processes, and network connections for malicious activity | App or agent-based detection — scans for malware, phishing URLs, rogue Wi-Fi, jailbreak exploits, and malicious apps on mobile |
| What it prevents | Unauthorized access, data leakage, unpatched OS, non-compliant devices, unauthorized apps | Malware execution, ransomware, fileless attacks, lateral movement, data exfiltration | Mobile malware, phishing links, man-in-the-middle attacks, jailbreak exploits, malicious app installs |
| What it cannot do | Detect malware, block phishing, inspect network traffic, analyze user behavior | Enforce device enrollment, push security policies, manage apps, enforce encryption baselines | Enforce device policies, manage enrollment, push apps, enforce compliance templates |
| Deployment | MDM server + device enrollment via zero-touch, QR code, or manual | Agent installed on endpoint + cloud-based detection console | App or SDK integrated into managed apps + cloud-based detection console |
| Typical vendors | Bento MDM, Hexnode, Scalefusion, Jamf, Microsoft Intune | CrowdStrike Falcon, SentinelOne, Microsoft Defender for Endpoint | Zimperium, Lookout, Wandera (Jamf Protect for Apple) |
The three tools are layers, not alternatives. MDM enforces the security baseline (prevention). EDR detects active threats on all endpoints (detection and response). MTD detects mobile-specific threats that EDR may not cover (mobile detection). Organizations with mature security programs run all three. Organizations starting their endpoint security journey typically deploy MDM first (cheapest, broadest coverage) and add MTD and EDR as the threat landscape and budget justify.
Which Compliance Frameworks Does MDM Security Address?
MDM security controls map to specific requirements in every major compliance framework governing mobile device use. The frameworks differ in scope and specificity, but they share common requirements that MDM enforces: encryption, access controls, audit logging, and incident response (remote wipe).
HIPAA: Encryption at rest and in transit for devices storing or transmitting ePHI. Access controls and audit logging for all ePHI access. Remote wipe for lost or compromised devices. Automatic session timeout. MDM enforces all of these through the security controls described above.
CJIS Security Policy: Advanced authentication (MFA minimum), encryption, centralized audit logging, session timeouts, role-based access control, media protection (remote wipe), and device tracking for CJI assets. MDM compliance templates for CJIS compliance automatically enforce these.
NIST SP 800-124: Mobile device security baseline covering device management, authentication, encryption, app management, and remote wipe. NIST 800-124 is the reference standard for federal agencies managing mobile devices.
CIS Benchmarks: OS-specific security hardening baselines for Android, iOS, Windows, and macOS. MDM compliance templates automatically apply CIS benchmarks to enrolled devices.
PCI-DSS: Encryption and access controls for devices that handle payment card data. Content filtering and data sharing restrictions prevent cardholder data from leaking through unauthorized channels.
SOC 2: Device security as part of the security trust service criteria. MDM audit logs, encryption enforcement, and access controls contribute evidence for SOC 2 assessments.
GDPR: Data protection controls for devices managing EU citizen data. Remote wipe ensures data can be erased on request. Work profiles ensure the separation of personal and corporate data on BYOD devices.
Bento MDM includes pre-built compliance templates for CIS, NIST, CJIS, and HIPAA at $1/device — no enterprise tier required for compliance baselines. For detailed CJIS mapping, see the MDM capabilities checklist. For detailed HIPAA mapping, see MDM for Healthcare.
Frequently Asked Questions
What is MDM security?
MDM security is the set of device-level controls that mobile device management enforces to protect corporate data on mobile endpoints. These controls include encryption enforcement, passcode and authentication requirements, VPN profiles, remote wipe and lock, automated patching, data loss prevention, and content filtering. MDM security is a prevention layer — it enforces the security baseline, reducing the attack surface. It does not detect active threats, so separate MTD or EDR tools are required.
Is MDM the same as endpoint security?
No. MDM is a subset of endpoint security focused on mobile device policy enforcement. Endpoint security is a broader discipline that includes MDM (device configuration and compliance), EDR (endpoint threat detection and response), MTD (mobile-specific threat detection), and endpoint protection platforms (EPPs) that combine prevention and detection. MDM provides the configuration and compliance layer. EDR and MTD provide the threat detection layer. Both are required for complete endpoint security.
Does MDM protect against malware?
Not directly. MDM does not scan for malware, analyze app behavior, or detect malicious code. MDM reduces malware risk indirectly by enforcing automated patching (eliminating known vulnerabilities), blocking unauthorized app installations (preventing sideloaded malware), and enforcing encryption (protecting data even if malware is present). To detect active malware on mobile devices, organizations deploy Mobile Threat Defense (MTD) tools alongside MDM.
What is the role of MDM in zero trust?
MDM provides the device verification layer in a zero-trust architecture. Before a device accesses corporate resources, MDM verifies its posture: is it enrolled? Is encryption active? Is the OS current? Is it jailbroken? Is the passcode compliant? Devices that fail posture checks are blocked automatically. MDM does not replace identity verification (IAM), network verification (ZTNA), or threat detection (MTD/EDR) — it complements them as the device-specific trust layer.
Can MDM enforce security policies when devices are offline?
Standard MDM security policies persist on the device once applied — encryption, passcodes, and app restrictions remain active even when the device loses connectivity. New policy changes and management commands cannot be delivered without connectivity. Bento MDM’s Offline QR Commands solve this: IT generates a QR code containing the policy update or command, the device scans it locally, and the command executes without a network connection. This extends MDM security enforcement to disconnected environments where no other MDM solution can operate.
Related Articles