What Is Mobile Device Management (MDM)? — A Complete Guide

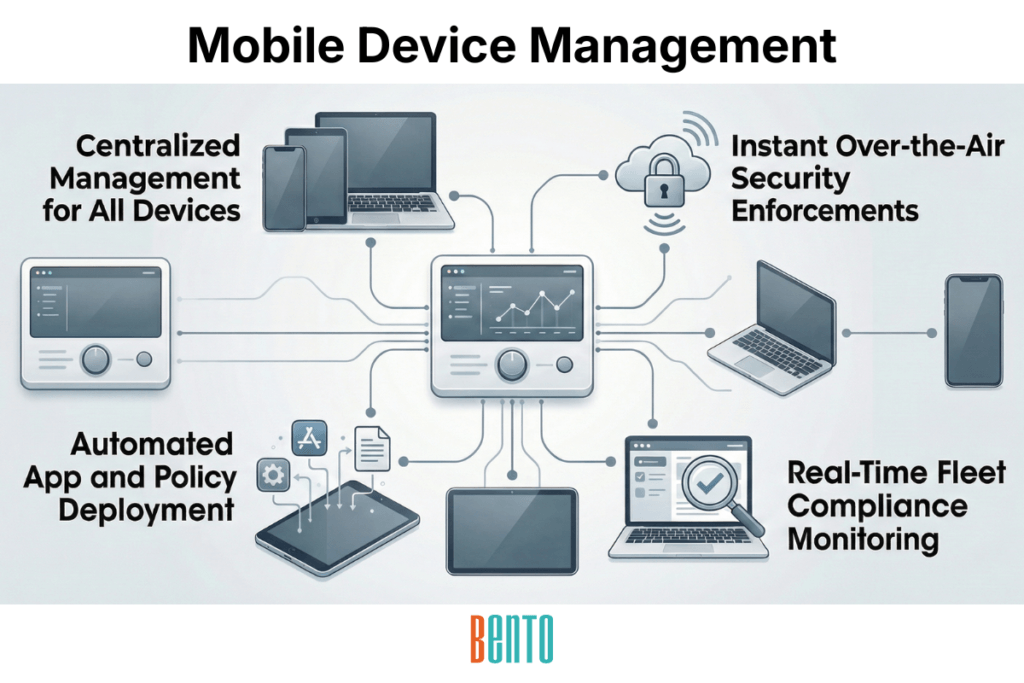
Mobile Device Management (MDM) is software that lets IT teams centrally enroll, configure, secure, and support mobile devices — smartphones, tablets, laptops, and ruggedized endpoints — over the air. MDM works by installing a lightweight agent or using native OS management APIs on each device, which communicates with a central console where administrators push policies, distribute apps, and monitor compliance in real time. Organizations deploy MDM in the cloud, on-premises, or in a hybrid model to enforce security policies, manage applications, and maintain regulatory compliance across their entire device fleet.
The concept is straightforward: instead of physically touching every device to configure it, MDM gives IT teams a single console to manage thousands of devices across multiple operating systems and locations. Whether your fleet is 50 smartphones or 50,000 mixed endpoints, MDM is the layer between your security policies and the devices that must follow them.
Solutions like Bento MDM extend mobile device management solutions further with cross-platform support (Android, iOS, Windows, macOS, Linux), flexible deployment (cloud, on-premise, SaaS), and pricing that starts at $1/device — making enterprise-grade MDM accessible to organizations of every size.
How Mobile Device Management Works
MDM operates through a server-client architecture. The MDM server — hosted in the cloud or on your own infrastructure — acts as the central command console. Each managed device runs either a lightweight MDM agent (on Android and Windows) or communicates through a native OS management framework (on iOS and macOS via Apple’s MDM protocol). The server pushes configurations, policies, and apps to devices over the air (OTA), and devices continuously report their status — health, compliance, location, installed apps — back to the server.
The workflow follows a cycle: enroll the device, push policies and apps, monitor compliance, respond to issues (remote lock, wipe, troubleshoot), and repeat as the fleet evolves. Every action — from deploying a Wi-Fi profile to wiping a stolen device — is performed in the admin console without anyone physically touching the endpoint.
Device Enrollment Methods
MDM enrollment is the process by which devices join the management system. Three primary methods exist, and the right choice depends on device ownership and scale:
- Automatic enrollment: Devices configure themselves on first boot with no IT intervention. Android uses Android Automatic Enrollment, Apple uses Automatic Device Enrollment (ADE, formerly DEP), and Windows uses Autopilot. This is the standard for corporate-owned fleets at scale.
- QR code or link enrollment: The user scans a QR code or clicks an enrollment link that installs the MDM profile. Common for BYOD programs where employees enroll their own devices.
- Manual enrollment: IT physically configures the device or walks the user through a setup wizard. Rare in modern deployments, but sometimes necessary for legacy or specialty devices.
What Devices Does MDM Manage?
Modern MDM manages endpoints via a management API or agent. This includes smartphones (Android, iOS), tablets (iPad, Android tablets, Windows tablets), laptops (Windows, macOS, Linux), ruggedized handhelds and scanners (field service, logistics, manufacturing), kiosk and POS terminals (retail, hospitality), and increasingly IoT devices and digital signage. The platforms supported by a typical MDM solution include Android, iOS, iPadOS, Windows, macOS, and Linux — though the depth of coverage varies by vendor. Some solutions, like Jamf, focus exclusively on Apple. Others, like Bento MDM, manage all six operating systems from a single console.
Core MDM Capabilities — What Mobile Device Management Should Be Able to Do
MDM capabilities define what the software can enforce, automate, and report on across your device fleet. Whether you’re building a requirements document, responding to an RFP, or evaluating vendors against a compliance framework like CJIS, these are the capabilities every MDM solution should deliver:
Enroll devices at scale: Support Automatic enrollment (Android Automatic, Apple ADE, Windows Autopilot) and QR-based enrollment for rapid fleet onboarding without manual configuration.
Enforce security policies: Push passcode requirements, encryption standards, VPN configurations, and Wi-Fi profiles to every managed device over the air.
Distribute and manage applications: Install, update, and revoke apps silently — including private enterprise apps through a managed app catalog or Enterprise App Store.
Track device location and health: Monitor GPS location, battery level, OS version, storage, and compliance status in real time across the entire fleet.
Enable remote actions: Lock, wipe, restart, and remotely view or control devices from the admin console — without dispatching a technician.
Support BYOD separation: Containerize corporate data using work profiles (Android) or managed app configurations (iOS) so personal data stays private and corporate data stays protected.
Maintain audit trails: Log every admin action, policy change, and compliance event centrally for regulatory audits and internal reviews.
Integrate with identity providers: Connect to Active Directory, LDAP, SAML, and OAuth providers for centralized authentication and user management.
Automate OS and app patching: Schedule and push OS updates and app patches automatically, keeping devices secure without relying on end users.
Apply compliance templates: Deploy pre-built security baselines for CIS Benchmarks, NIST frameworks, and CJIS Security Policy requirements — rather than building policies from scratch.
Support kiosk and single-app mode: Lock devices to a single application (COSU) or a set of approved applications for retail POS, patient check-in, digital signage, or field service use cases.
Enforce content filtering and data sharing controls: Block access to unauthorized websites, prevent data leakage between corporate and personal apps, and disable screen capture in sensitive contexts.
Bento MDM includes all 12 capabilities above across all pricing tiers — nothing is gated behind an enterprise add-on. This matters because organizations often discover that critical features, such as compliance templates or remote control, require upgrades with other vendors.
MDM Deployment Models
MDM deployment determines where the server runs and who manages the infrastructure. Three models exist, and the right choice depends on your compliance requirements, IT resources, and data sovereignty needs.
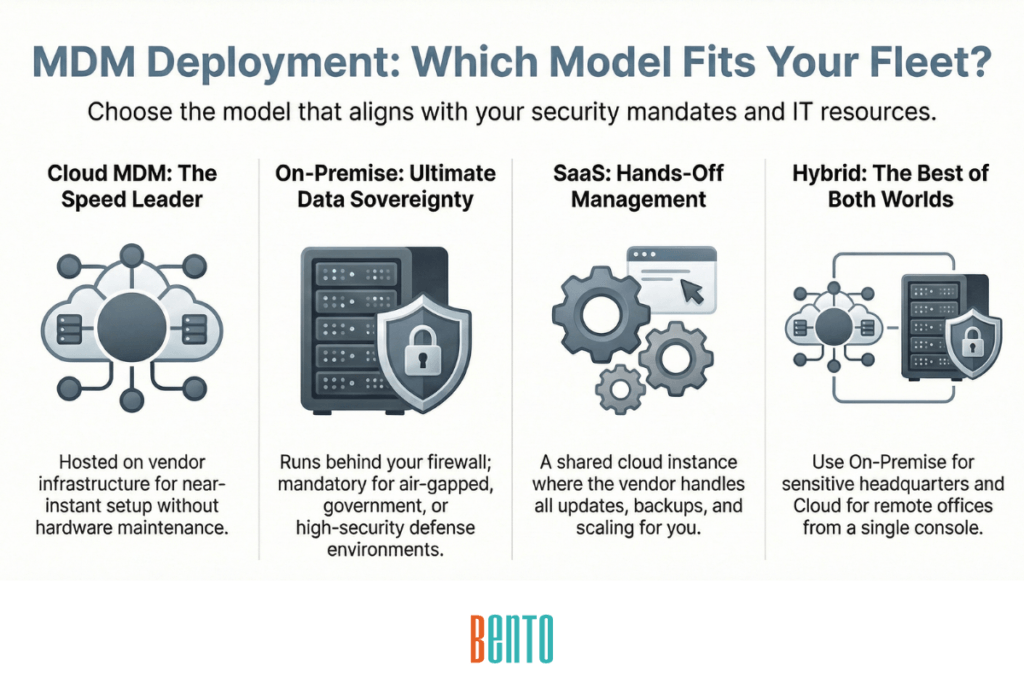
Cloud MDM
The MDM server runs on the vendor’s cloud infrastructure (or a major cloud provider like AWS, Azure, or GCP). Your IT team manages devices through a web-based cloud MDM console without maintaining any server hardware. This is the fastest deployment model — setup takes minutes — and the most common choice for organizations without strict data residency requirements.
On-Premise MDM
The MDM server runs entirely within your own infrastructure — your data center, your firewall, your network. No device data ever leaves your premises. This model is required by organizations in government, defense, healthcare, and finance that operate under data sovereignty mandates or need air-gapped environments. On-premise MDM requires more IT resources to maintain, but gives you complete control over data, access policies, and integration.
SaaS MDM
A shared cloud instance managed entirely by the vendor. Your IT team uses the platform without any infrastructure responsibility — updates, backups, and scaling are handled for you. SaaS MDM is the simplest option for small and mid-sized teams that want enterprise capabilities without the operational overhead.
Bento MDM is one of the few solutions that offers all three deployment models with the same admin experience across them. Organizations that need maximum flexibility — on-premise for headquarters, cloud for remote offices — can run hybrid deployments from a single console.
Benefits of Mobile Device Management
MDM delivers measurable operational and security improvements for IT teams managing device fleets of any size. The primary benefits include:
- Reduced IT overhead: Automate enrollment, patching, and configuration instead of touching each device manually. Automatic enrollment alone eliminates the setup bottleneck that slows every new hire’s first day.
- Stronger endpoint security: Enforce encryption, passcodes, remote wipe, and app controls across every device — consistently and at scale. A lost laptop with MDM-enforced encryption and remote wipe capability is an inconvenience, not a data breach.
- Faster compliance: Pre-built compliance templates for CIS, NIST, CJIS, HIPAA, and SOC 2 get you audit-ready without building policies from scratch. Audit logs automatically track every admin action.
- Improved productivity: Employees get their devices configured with the right apps, VPN profiles, and Wi-Fi settings on first boot. Less time waiting for IT setup means more time working.
- Lower support costs: Remote view, remote control, and remote troubleshooting eliminate the need for most on-site support visits. IT resolves issues in minutes from the console, rather than dispatching technicians.
- Scalable fleet management: Adding 10 devices or 10,000 devices follows the same Automatic workflow. MDM scales with your organization without increasing your IT headcount in proportion.
- BYOD without compromise: Work profiles and containerization let employees use their own devices for work while keeping corporate data separate and protected. Privacy for the user, control for IT.
MDM Security Controls
MDM is, at its core, a security monitoring tool. Every capability — enrollment, policy enforcement, app management, remote wipe — exists to protect corporate data on devices that IT cannot physically control. The security controls MDM provides include:
Passcode and biometric enforcement. MDM sets minimum passcode complexity, lockout thresholds, and biometric authentication requirements. Devices that fail to meet these standards are flagged or blocked from accessing corporate resources.
Encryption at rest and in transit. MDM enforces full-disk encryption on every managed device and pushes VPN profiles to encrypt data in transit. Combined with per-app VPN configurations, this ensures corporate traffic never crosses an unprotected network.
Remote wipe and lock. When a device is lost, stolen, or compromised, IT can lock it instantly or wipe it — either selectively (corporate data only) or completely (a full factory reset). Factory reset protection prevents unauthorized resets from removing the MDM profile.
Zero-trust posture checks. Before granting access to corporate resources, MDM can verify device health: is the OS up to date? Is the device jailbroken? Is it in an approved location? Non-compliant devices are blocked automatically. For a deep dive into MDM’s 7 security layers and how they fit into zero-trust architecture, see MDM Security.
Bento MDM adds a unique platform capability: Offline QR Commands. Even when a device has no internet connectivity — in a mine, on a ship, in a disaster recovery zone — IT can enforce policies and push fixes by generating a QR code that the device scans locally. No competitor offers this.
For regulated industries, MDM security controls map directly to compliance frameworks. HIPAA requires encryption and access controls for devices handling protected health information. CJIS requires advanced authentication and audit logging for devices accessing criminal justice data. NIST and CIS Benchmarks provide security baselines that MDM compliance templates enforce automatically. PCI-DSS requires encryption and access controls for devices that handle payment data. GDPR requires data protection controls for devices managing EU citizen data.
MDM vs MAM vs EMM vs UEM — What Is the Difference?
MDM is one of several overlapping terms in the endpoint management space. Understanding the differences helps you choose the right scope for your organization:
| Attribute | MDM Mobile Device Management |
MAM Mobile Application Management |
EMM Enterprise Mobility Management |
UEM Unified Endpoint Management |
|---|---|---|---|---|
| What it manages | The device itself — OS settings, security policies, encryption, connectivity | Individual applications — install, update, configure, revoke, enforce per-app policies | Devices + apps + content — combines MDM, MAM, and mobile content management (MCM) | All endpoints — smartphones, tablets, laptops, desktops, IoT, wearables, printers, kiosks |
| Scope | Mobile devices only (phones, tablets, some laptops) | App-level only — does not control the underlying device | Mobile devices + apps + documents — broader than MDM, narrower than UEM | Every endpoint type across the organization — the broadest scope |
| Device control level | Full device — passcodes, encryption, remote wipe, VPN, Wi-Fi, kiosk mode | App container only — data stays in the managed app, no control over device settings | Full device + app-level policies + content distribution | Full device + app + content + desktop/IoT management under one platform |
| BYOD suitability | Good — work profiles separate corporate from personal data | Best for BYOD — IT manages only the app, not the personal device | Strong — supports both device-level and app-only management per policy | Strong — same BYOD capabilities as EMM, extended to non-mobile endpoints |
| Security capabilities | Encryption enforcement, remote wipe, factory reset protection, VPN profiles, zero-trust posture checks | Per-app VPN, app-level data loss prevention, managed app configurations | All MDM + MAM security features combined, plus secure document distribution | All EMM security features extended to desktops, servers, and IoT endpoints |
| Enrollment method | Zero-touch (Autopilot, ADE, Android ZT), QR code, manual | App-based — user installs a managed app or workspace from the app store | Device enrollment (MDM path) or app enrollment (MAM path) depending on policy | All MDM enrollment methods + OS-native desktop enrollment (GPO, SCCM, Intune agent) |
| Best for | Organizations managing corporate-owned mobile fleets with full device control requirements | BYOD-heavy environments where IT needs app control without managing the personal device | Organizations needing both device and app management with secure content distribution | Large enterprises managing a mix of mobile, desktop, IoT, and specialty endpoints from one console |
| Typical examples | Bento MDM, Hexnode, Scalefusion, SOTI MobiControl | Microsoft Intune MAM, Citrix Endpoint Management (app-only mode) | VMware Workspace ONE, ManageEngine Mobile Device Manager Plus | Microsoft Intune (full UEM), VMware Workspace ONE UEM, Bento MDM (MDM + desktop management) |
| Relationship to MDM | — | MAM is a subset that can operate independently or alongside MDM | EMM is MDM + MAM + MCM combined into a broader management approach | UEM is EMM expanded to include all endpoint types, not just mobile |
MDM (Mobile Device Management): Manages the device itself — enrollment, policies, security settings, OS updates. MDM controls what the device can do and how it’s configured. This is the foundation layer. For how MDM compares to RMM (Remote Monitoring and Management), see the MDM vs RMM guide.
MAM (Mobile Application Management): Manages individual applications rather than the entire device. MAM controls which apps can be installed, how they share data, and whether they require VPN access. MAM is often used alongside MDM for granular app-level control, especially in BYOD environments where IT doesn’t want to manage the whole device.
EMM (Enterprise Mobility Management): A broader category that combines MDM, MAM, and mobile content management (MCM) into a unified approach. EMM manages devices, apps, AND the content/data on those devices. Most modern MDM solutions have evolved to include EMM capabilities.
UEM (Unified Endpoint Management): The broadest scope — UEM manages not just mobile devices but all endpoints: desktops, laptops, printers, IoT devices, wearables, and digital signage. UEM is the evolution of MDM + EMM into a platform that covers every device type an organization uses.
In practice, the lines between these categories have blurred. Most MDM solutions marketed today include MAM and EMM capabilities. Whether you need full UEM depends on whether your fleet includes non-mobile endpoints, such as desktops and IoT devices. Bento MDM, for example, manages mobile devices, laptops, desktops, and ruggedized endpoints from a single console — functioning as both MDM and UEM depending on how you deploy it.
MDM Use Cases by Industry
MDM requirements vary by industry because the devices, compliance mandates, and operational workflows differ. Here is how MDM applies across the verticals that depend on it most:
Healthcare
Hospitals and clinics manage shared tablets at nurses’ stations, mobile carts, and clinician-facing devices that access electronic health records. MDM for healthcare enforces HIPAA-compliant encryption, passcode policies, and data containerization to protect patient health information (PHI). Shared Device Mode lets multiple clinicians use the same tablet with isolated sessions, and remote wipe protects PHI if a device is lost.
Government and Defense
Government agencies and defense contractors require air-gapped deployment, CJIS compliance, advanced authentication, and centralized audit logging. On-premise MDM for government keeps device data entirely within government infrastructure. Role-based access control restricts admin actions to authorized personnel, and compliance templates automatically enforce NIST and CIS Benchmark standards.
Retail and Hospitality
Retail chains manage POS terminals, inventory scanners, customer-facing kiosks, and digital signage across dozens or hundreds of locations. MDM kiosk mode locks devices to approved applications, content filtering blocks unauthorized browsing, and remote management keeps every terminal configured consistently without sending IT staff to each store.
Field Services and Utilities
Field technicians use ruggedized tablets and handhelds that operate in environments with limited or no connectivity. Field service MDM provisions these devices with diagnostic tools, route-planning apps, and maintenance forms—and offline mode ensures policies stay enforced even when the device can’t reach the server.
Education
Schools and universities manage student iPads, Chromebooks, and laptops in 1:1 device programs. MDM enforces content filtering for CIPA compliance, controls which apps students can install, and supports shared device carts where multiple students use the same device throughout the day. Exam lockdown mode restricts devices to a testing app during assessments.
How to Choose the Right MDM Solution
MDM solutions vary significantly in scope, pricing, and platform coverage. When evaluating vendors, these are the decision criteria that matter most:
- Platform coverage: Does the solution manage all the operating systems in your fleet? Some vendors (Jamf, Mosyle, Kandji) focus exclusively on Apple. Others (Scalefusion, Hexnode) are Android-heavy. If your fleet spans Android, iOS, Windows, and macOS, you need a solution that manages them all from a single console.
- Deployment options: Do you need cloud-only, on-premise, or both? Most vendors offer cloud. Few offer true on-premises deployment—and even fewer offer hybrid (on-premises for sensitive environments, cloud for remote offices).
- Security features: Compare the security controls: passcode enforcement, encryption, remote wipe, VPN profiles, zero-trust posture checks, and factory reset protection. Look for compliance templates (CIS, NIST, CJIS) rather than building policies manually.
- Pricing model: MDM pricing typically runs on a per-device/month or per-user/month basis. Some vendors gate critical features behind enterprise tiers. Evaluate what’s included at the base price versus what requires an upgrade.
- Scalability: Can the solution grow from your current fleet size to 10x without re-architecting? Does enrollment scale with Automatic, or does each new device require manual setup?
- Support and integration: Does the vendor support your identity provider (AD, LDAP, Okta, Azure AD)? Is there REST API access for custom integrations? What does support look like — chat, phone, dedicated account manager?
Bento MDM checks every criterion above: six operating systems from one console, three deployment models (cloud, on-premise, SaaS), full security controls at every tier, $1/device pricing with no feature gating, Automatic enrollment for unlimited scale, and REST API access for custom integration. That combination of breadth and affordability is rare in the MDM market.
MDM Best Practices
MDM best practices determine whether your deployment runs smoothly at scale or creates friction that drives users and admins to workarounds. These are the practices that experienced IT teams follow:
- Start with a device policy before choosing software. Define what you need to manage (platforms, ownership models, compliance requirements) before evaluating vendors. The policy drives tool selection, not the other way around.
- Use Automatic enrollment for every new device. Manual enrollment does not scale. Whether you’re onboarding 5 devices or 5,000, Automatic (Autopilot, ADE, Android Automatic) should be the default path.
- Separate corporate and personal data on BYOD devices. Work profiles and containerization protect corporate data without invading employee privacy. This is non-negotiable for BYOD programs. See BYOD vs. COPE vs. CYOD for a complete comparison of ownership models.
- Automate patching. Do not rely on end users to install OS and app updates. MDM should push patches automatically on a schedule you control, with rollback capability if an update causes issues.
- Apply compliance templates; do not build from scratch. CIS Benchmarks, NIST frameworks, and CJIS templates exist for a reason. Use them as your baseline and customize from there.
- Monitor device health continuously, not on a schedule. Real-time compliance monitoring catches issues before they become incidents. Dashboard alerts for non-compliant devices should trigger automatic remediation or admin notification.
- Use RBAC to limit admin access by role. Not every IT team member needs the same level of console access. Role-based access control prevents accidental or unauthorized changes and creates accountability.
- Test policies on a pilot group before fleet-wide rollout. Push new configurations to a small test group first. Verify that nothing breaks before deploying to the entire fleet.
- Document your MDM policy and train users. A policy that exists only in the admin console is invisible to the people it affects. Document acceptable use, BYOD rules, and incident response procedures. Train new hires during onboarding.
- Review and update policies quarterly. Device threats, compliance requirements, and organizational needs evolve. A quarterly review ensures your MDM configuration stays aligned with reality.
Frequently Asked Questions
What is mobile device management in simple terms?
Mobile device management is software that lets IT teams manage, secure, and support smartphones, tablets, and laptops from a central console — without physically touching each device. IT pushes settings, apps, and security policies over the air, and devices report their status back.
Is MDM the same as mobile security?
No. MDM is a device-centric management framework that includes security controls as one component. Mobile security is broader and can include threat detection, network security, and endpoint protection that exist outside the MDM platform. MDM provides the foundational layer — encryption enforcement, passcode policies, remote wipe — that mobile security strategies depend on.
Can MDM manage both company-owned and personal devices?
Yes. Company-owned devices run in fully managed or kiosk (COSU) mode with complete IT control. Employee-owned devices (BYOD) are enrolled with work profiles that isolate corporate data from personal data. IT manages the corporate container without accessing personal apps, photos, or messages.
What does CJIS require from an MDM solution?
The CJIS Security Policy requires advanced authentication (MFA at minimum), encryption at rest and in transit, centralized audit logging that records all access to criminal justice information, session timeouts, and role-based access control. MDM compliance templates for CJIS enforce these requirements automatically across managed devices.
How much does MDM cost?
MDM pricing varies widely. Enterprise platforms such as VMware Workspace ONE and Microsoft Intune often bundle MDM with broader licensing packages. Dedicated MDM vendors typically charge $1–10 per device per month, depending on features and scale. Bento MDM starts at $1/device with all features included — no enterprise tier gating.
Related Articles