MDM vs MAM — What Is the Difference and Which Do You Need?
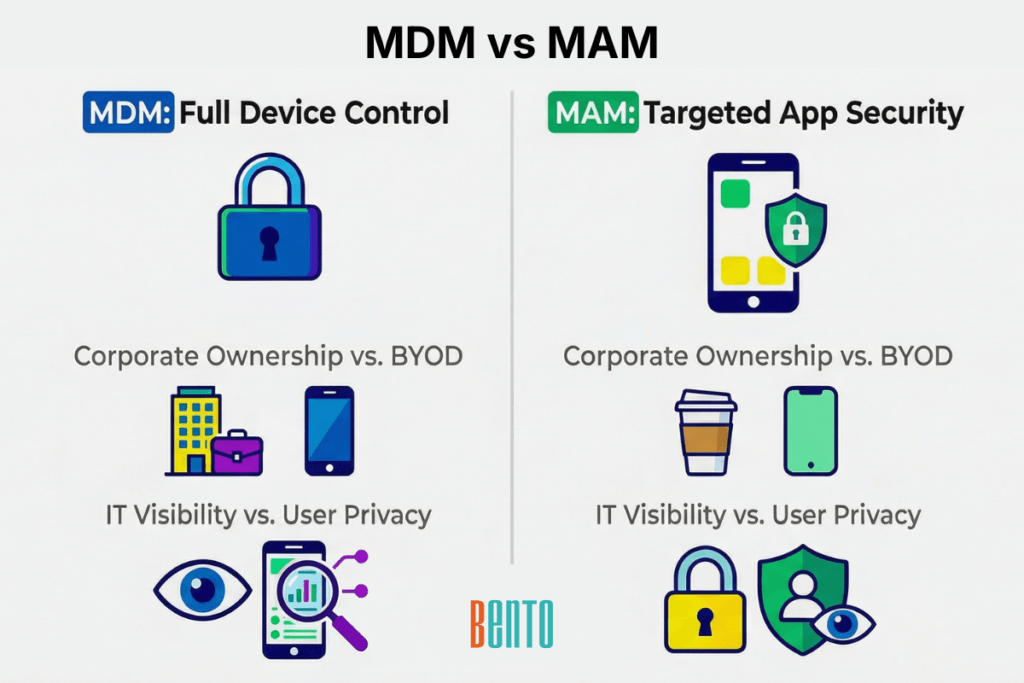
MDM manages the device. MAM manages the application. That is the core difference between Mobile Device Management and Mobile Application Management — and it determines how much control IT has, how much privacy employees keep, and whether your organization needs one, the other, or both.
The MDM vs MAM question comes up most often in BYOD decisions. When employees use their own phones for work, IT has to choose: enroll the entire device and manage it at the OS level (MDM), or manage only the corporate apps and leave the personal device untouched (MAM). The right answer depends on your compliance requirements, your device ownership model, and the level of friction your employees are willing to tolerate.
This guide defines both and compares them across eight dimensions, and provides a decision framework for choosing the right approach.
What Is MDM and What Is MAM?
Mobile Device Management (MDM) is software that gives IT teams centralized control over devices — their operating systems, security settings, encryption, connectivity, installed apps, and hardware capabilities. MDM solutions enroll the device into a management platform, pushe policies over the air, and can remotely lock, wipe, or troubleshoot it. IT sees and controls the entire device. This is the standard approach for corporate-owned fleets where the organization owns the hardware and sets all the rules.
Mobile Application Management (MAM) is software that gives IT teams control over specific applications on a device — without managing the device itself. MAM controls which corporate apps are installed, how those apps share data, whether app traffic routes through a VPN, and whether corporate data can be copied outside the managed app container. IT sees and controls only the managed apps. Everything else on the device — personal apps, photos, browsing history, location — remains invisible to IT. This is the approach organizations use when they need to protect corporate data on devices they do not own.
The distinction matters because it shapes the user experience, the IT workload, and the security model. MDM gives IT maximum control at the cost of employee privacy. MAM gives employees maximum privacy at the cost of IT control. Most enterprises end up using both — MDM for company-owned devices and MAM for BYOD — but the decision starts with understanding what each actually does.
Bento MDM includes application management capabilities — Enterprise App Store, per-app VPN, managed app configurations, and selective app data wipe — so IT teams get both MDM and MAM controls from a single console without needing a separate MAM tool.
MDM vs MAM — How They Compare
The table below compares MDM and MAM across the eight attributes that matter most for IT decision-making. Each cell is written as a standalone statement — so the comparison holds whether you read the full table or a single row.
| Attribute | MDM Mobile Device Management |
MAM Mobile Application Management |
|---|---|---|
| What it manages | The device itself — OS settings, security policies, encryption, connectivity, device hardware | Individual applications — install, configure, restrict, wipe app data, enforce app-level policies |
| Scope of control | Full device — IT controls everything on the device | App container only — IT controls only managed applications, nothing else |
| Enrollment method | Device-level via zero-touch (ADE, Autopilot, Android ZT), QR code, or manual enrollment | App-level — user installs a managed app or workspace, no device enrollment required |
| Security approach | Device-level encryption, passcode enforcement, VPN profiles, remote device wipe, factory reset protection | Per-app VPN, app-level DLP (copy/paste and open-in restrictions), selective app data wipe |
| BYOD handling | Work profiles containerize corporate data on the enrolled device — IT still manages the device | IT manages only the app container — no visibility into or control over the personal device |
| Data separation | Work profile (Android) or managed configuration (iOS) separates corporate and personal at device level | App-level containment — corporate data stays inside managed apps, personal apps are untouched |
| User privacy impact | Higher — IT can see device location, installed apps, OS version, and enforce device-wide policies | Lower — IT sees only managed app activity, no access to personal apps, photos, or messages |
| Best for | Corporate-owned devices, kiosks, shared devices, regulated environments needing full device control | BYOD-heavy organizations, contractor devices, environments where employees refuse device enrollment |
The table makes the trade-off clear: MDM gives IT more control, MAM gives employees more privacy. Neither is universally better. The right choice depends on who owns the device and what compliance requirements apply.
When to Use MDM, When to Use MAM, and When You Need Both
The MDM vs MAM decision is not a product choice — it is a policy decision that flows from three questions: Who owns the device? What data does it access? What regulations apply?
Use MDM When You Need Full Device Control
MDM is the default when the organization owns the device. Corporate-purchased smartphones, tablets issued to field workers, kiosk terminals, shared clinical devices, ruggedized warehouse scanners — if your organization bought it, IT should manage it at the device level.
MDM is also required when compliance mandates device-level security controls. CJIS requires full-disk encryption and device tracking. HIPAA requires encryption at rest for devices that store protected health information. PCI-DSS requires access controls for devices that handle payment data. These requirements can only be met at the device level — app-level controls are not sufficient.
If you are managing corporate-owned devices in a regulated industry, MDM is not optional. It is the minimum.
Use MAM When You Only Need to Manage Applications
MAM without device enrollment makes sense in three scenarios. First, BYOD programs where employees refuse to enroll their personal phones. Some employees will never accept IT having visibility into their personal devices — and if enrollment is mandatory, they will stop using their phones for work, which defeats the purpose of BYOD. MAM lets IT protect corporate email, files, and apps without touching any personal data.
Second, contractor and temporary worker devices. If someone works for your organization for 90 days and uses their own laptop, enrolling their device in your MDM creates friction on both ends — enrollment on day one, deprovisioning on day 90, and privacy concerns in between. MAM lets you push a managed app container, revoke it on the last day, and never touch their device.
Third, organizations where the only corporate assets on the device are email and a few cloud apps. If your employees access Outlook, Teams, and a CRM on their phones — and nothing else — MAM protects those specific apps without the overhead of full device management.
Use Both MDM and MAM When Compliance Demands It
The most common enterprise pattern is not “MDM or MAM” — it is “MDM and MAM together.” Corporate-owned devices get full MDM enrollment with device-level policies. BYOD devices get MAM-only enrollment with app-level policies. Some high-risk BYOD devices — those accessing PHI, financial data, or classified information — get both: device enrollment for encryption and compliance, plus app-level containment for data loss prevention.
This dual approach enables IT to enforce a consistent security baseline across all devices while respecting ownership boundaries. The corporate phone and the employee’s personal phone both protect corporate data, but through different mechanisms tailored to their respective ownership models.
Solutions like Bento MDM, which include both MDM and MAM capabilities in a single console at $1/device, make this dual approach operationally simple. IT does not need two separate tools, two dashboards, or two licensing agreements. One platform manages devices at the MDM level and applications at the MAM level, with the enrollment path determined by policy.
How MDM and MAM Handle Security Differently
MDM security operates at the device level. It enforces full-disk encryption, so all data on the device is protected at rest. It pushes VPN profiles so all data in transit routes through encrypted tunnels. It sets passcode complexity requirements so unauthorized users cannot unlock the device. It enables remote wipe, so a lost device can be erased before data is exposed. And it enforces factory reset protection, so a wiped device cannot be reactivated without managed credentials.
MAM security operates at the application level. It enforces per-app VPN so only corporate app traffic is encrypted — personal browsing is not routed through the corporate VPN. It restricts copy-paste between managed and unmanaged apps, preventing corporate data from leaking into personal messaging or cloud storage. It applies managed app configurations so corporate apps connect to the right servers and authenticate correctly without the user entering credentials manually. And it enables selective app wipe so IT can erase corporate app data on an employee’s device without touching personal photos, messages, or apps, aka content filtering.
The critical distinction: MDM protects the device. MAM protects the data inside specific applications. For maximum security — especially in regulated industries — you layer both. Device-level encryption ensures data is protected if the device is stolen. App-level containment ensures data is protected if the user shares it inappropriately.
MDM vs MAM for BYOD — The Real Decision
On corporate-owned devices, MDM is always the answer. The organization owns the hardware, sets the rules, and needs full device-level control. The MDM vs MAM question only becomes a real decision when employees bring their own devices.
The BYOD decision tree comes down to three questions:
Does the device access regulated data (PHI, CJI, PCI data)? If so, you likely need MDM with work profiles — app-level controls alone may not meet the compliance requirements for device-level encryption and tracking.
Will employees accept device enrollment? If employees are willing to enroll their personal phones with a work profile that separates corporate and personal data, MDM with BYOD work profiles is the strongest approach. If they refuse, MAM without enrollment is the only viable path.
What corporate assets does the device access? If the device only accesses email and a cloud CRM, MAM is sufficient if it accesses internal file shares, VPN-protected resources, or sensitive databases, MDM’s device-level VPN and encryption become necessary.
Bento MDM’s work profile support on Android and managed app configurations on iOS give IT application-level control — similar to standalone MAM — without requiring a separate tool. For BYOD programs, this means IT can start with app-level management for most employees and escalate to full device enrollment for high-risk users, all from the same console.
For a comparison of BYOD against other ownership models like COPE and CYOD, see BYOD vs COPE vs CYOD.
Frequently Asked Questions
Can MAM work without MDM?
Yes. MAM can operate independently without device-level enrollment. The user installs a managed app or workspace on their device, and IT controls only that application container. This is the standard approach for BYOD programs, where employees will not accept full device enrollment. The trade-off: IT cannot enforce device-level encryption, passcode policies, or remote device wipe — only app-level controls apply.
Is MAM more privacy-friendly than MDM?
Yes. MAM gives IT visibility only into managed applications. Personal apps, photos, browsing history, and device location are not accessible to IT. MDM gives IT broader visibility — device location, installed app inventory, OS version, compliance status — even when work profiles separate corporate and personal data. For employees who prioritize privacy, MAM creates less friction.
Does Intune use MDM or MAM?
Microsoft Intune supports both MDM and MAM as separate enrollment paths. Devices can be fully enrolled (MDM) for device-level management, or users can access managed apps through Intune’s App Protection Policies (MAM) without device enrollment. Many organizations use Intune in both modes simultaneously — MDM for corporate devices, MAM for BYOD. Bento MDM provides the same dual-path capability from a single console.
Which is better for HIPAA compliance — MDM or MAM?
MDM is the safer choice for HIPAA. The HIPAA Security Rule requires encryption at rest on devices storing protected health information, access controls, and audit logging — requirements that map to device-level controls. MAM alone can protect data within managed applications, but cannot enforce device-level encryption or passcode policies. Most healthcare organizations use MDM on clinical devices and layer MAM on top for app-level data containment.
Can one platform handle both MDM and MAM?
Yes. Most modern MDM platforms include MAM capabilities such as application distribution, per-app VPNs, managed app configurations, and selective app wipe. Bento MDM manages devices at the MDM level and applications at the MAM level from the same admin console, with the enrollment path (device or app-only) determined by policy per user group. This eliminates the need for separate MDM and MAM tools.
Related Articles