What Mobile Device Management Should Be Able to Do — The Complete Capabilities Checklist
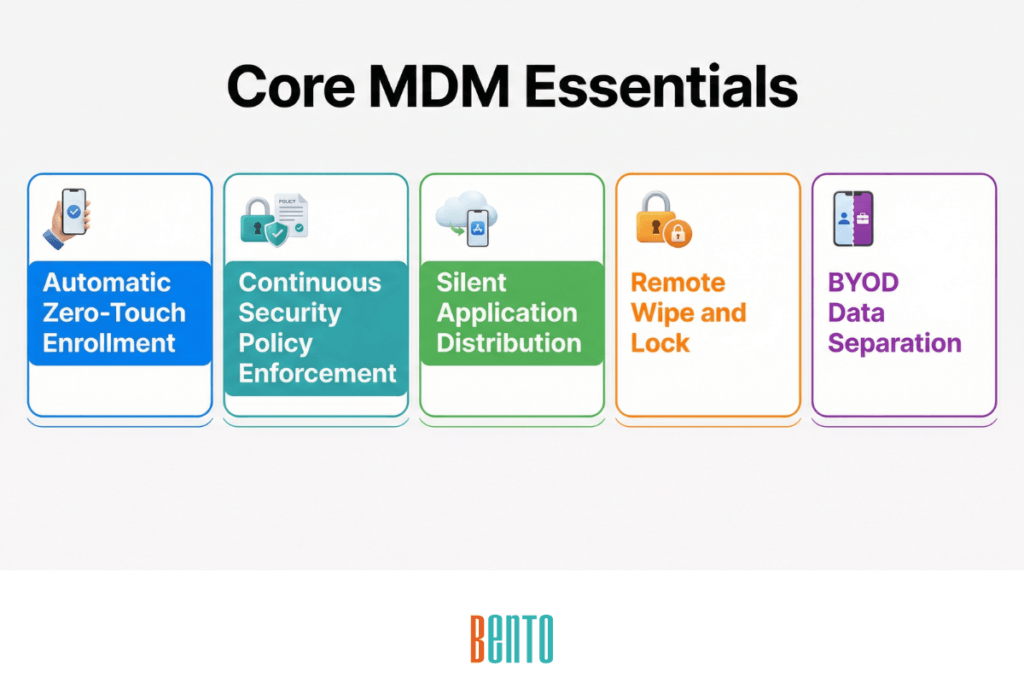
Mobile device management (MDM) should be able to enroll devices at scale, enforce security policies over the air, distribute and manage applications, monitor device health in real time, and execute remote actions like lock and wipe — all from a single console. That is the baseline. Any solution that cannot do all of these is incomplete.
But the baseline is not a buying decision. The differences between MDM solutions show up in how they handle BYOD, which compliance frameworks they support out of the box, whether they work in offline or air-gapped environments, and whether critical capabilities are included at every pricing tier or gated behind an enterprise upgrade.
This checklist covers the 12 core capabilities every MDM solution must have, maps them to CJIS Security Policy requirements for regulated organizations, and provides evaluation criteria for comparing vendors. If you are building a requirements document, filling out an RFP, or shortlisting MDM vendors, this is the reference.
The 12 Core Capabilities Every MDM Solution Must Have
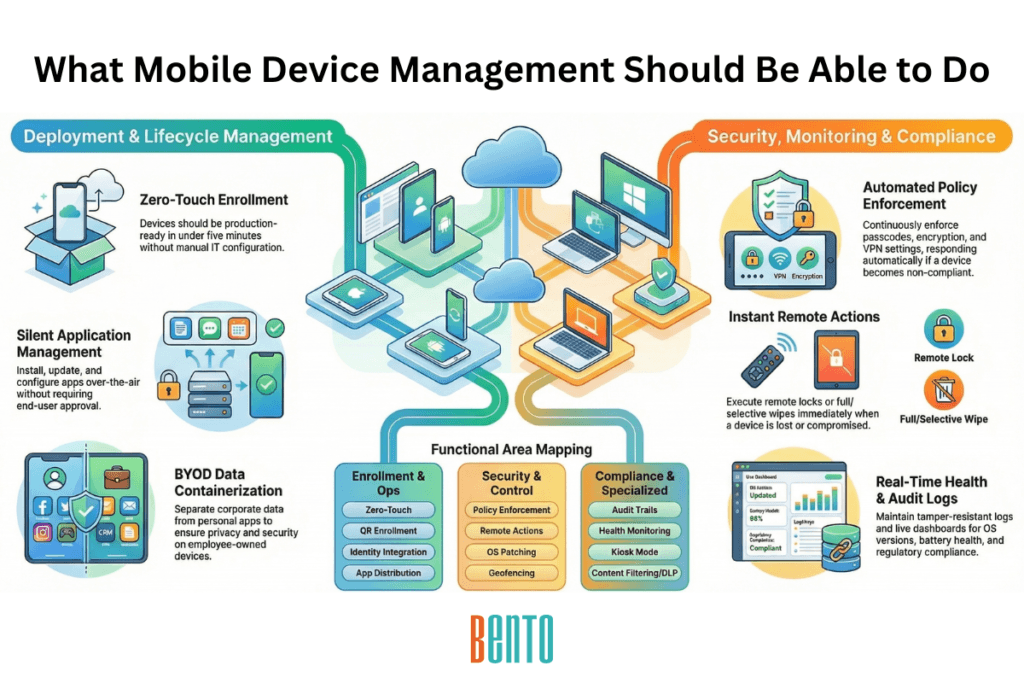
MDM capabilities fall into four functional areas: enrollment, security, operations, and compliance. The checklist below covers all four. Each capability is something mobile device management should be able to do regardless of vendor, platform, or deployment model.
1. Automatic Device Enrollment
MDM should automatically enroll devices on first boot — without manual configuration by IT or the end user. This means support for Android Zero-Touch Enrollment, Apple Automated Device Enrollment (ADE), and Windows Autopilot. Devices ship directly from the vendor or distributor, power on, connect to Wi-Fi, and pull their MDM profile, policies, and apps without intervention.
For organizations that cannot use zero-touch programs, the MDM should also support QR code enrollment — a fallback that still avoids full manual setup. The test: can a non-technical employee unbox a device and have it production-ready in under five minutes?
2. Security Policy Enforcement
MDM should be able to push security policies to every managed device over the air and enforce them continuously — not just at enrollment. This includes passcode complexity requirements and lockout thresholds, full-disk encryption enforcement, VPN profile deployment (including per-app VPN and always-on VPN), Wi-Fi profile configuration with certificate-based authentication, and automatic device lock after idle timeout.
Policies must apply consistently across Android, iOS, Windows, and macOS. If a device falls out of compliance — a user disables their passcode, the OS is outdated, the device is jailbroken — the MDM should detect it and respond automatically: alert the admin, restrict access, or quarantine the device.
3. Application Distribution and Management
MDM should be able to install, update, configure, and revoke applications across the entire fleet silently — without requiring the end user to approve or initiate anything. This includes pushing private enterprise apps that are not on public app stores, managing a curated Enterprise App Store for self-service, enforcing per-app VPN so corporate app traffic routes through encrypted tunnels, applying managed app configurations (pre-filled settings, server URLs, authentication tokens), and blocking unauthorized apps via allowlists or blocklists.
The application management layer is where MDM and MAM (Mobile Application Management) overlap. If your MDM cannot handle app-level controls, you will need a separate MAM tool, which adds cost, complexity, and another console to manage.
4. Device Health and Compliance Monitoring
MDM should be able to monitor every managed device in real time and report on health, compliance status, and security posture. This means dashboards showing OS version distribution across the fleet, battery and storage health, installed app inventory, compliance status per policy (pass/fail per device), and devices that have not checked in within a defined period.
Monitoring is only useful if it triggers action. The MDM should generate alerts when devices fall out of compliance, support automated remediation (push a missing policy, force an OS update), and produce exportable reports for audit and review.
5. Remote Device Actions
MDM should be able to execute critical management actions on any device remotely, from the admin console. The core remote actions are: remote lock (immediately lock the screen and require credentials to unlock), remote wipe — selective (corporate data and profiles only, personal data untouched) or full (factory reset), remote restart, and remote view and control (see the device screen live and interact with it for troubleshooting).
Remote wipe is the action that matters most in a security incident. When a device is lost, stolen, or compromised, the time between detection and wipe determines whether corporate data is exposed. Factory reset protection should prevent the wiped device from being reactivated without managed credentials.
See MDM Security for how these controls work together as a layered security stack.
Bento MDM adds a capability no other vendor offers: Offline QR Commands. When a device has no internet connectivity — in a mine, on a ship, in a disaster recovery zone — IT generates a QR code that the device scans to execute management commands locally. No network required.
6. BYOD Data Separation
MDM should be able to separate corporate data from personal data on employee-owned devices without giving IT visibility into personal apps, photos, or messages. On Android, this means Work Profile support — a managed container that holds corporate apps, email, and data in an isolated partition. On iOS, this means managed app configurations and Managed Open In restrictions that prevent data from flowing between corporate and personal apps.
The BYOD question is binary: either your MDM can containerize corporate data without invading personal privacy, or it cannot. If it cannot, your BYOD program will face employee resistance, legal risk, and enrollment avoidance.
7. Audit Trail and Compliance Logging
MDM should be able to log every administrative action, policy change, device event, and compliance status change in a centralized, tamper-resistant audit trail. This includes who made the change (admin user ID), what was changed (policy, app, configuration), when it happened (timestamp), and what device or device group was affected.
Audit logs serve two purposes: internal accountability (preventing unauthorized or accidental changes) and external compliance (demonstrating to auditors that security controls are enforced and documented). Logs should be exportable in standard formats (CSV, PDF) and retained for a configurable period that meets your regulatory requirements.
8. Identity Provider Integration
MDM should be able to integrate with your existing identity infrastructure for centralized authentication and user management. This means native support for Active Directory and LDAP (on-premise directory services), SAML and OAuth (SSO and federated identity), and SCIM (automated user provisioning and deprovisioning).
When an employee joins the organization, their directory account should automatically provision their device with the correct policies, apps, and access. When they leave, deprovisioning should immediately revoke access and trigger a selective wipe. MDM that operates outside your identity infrastructure creates manual work and security gaps at every employee lifecycle event.
9. Automated OS and App Patching
MDM should automatically schedule, push, and enforce operating system and application updates across the fleet. This means setting patching windows (deploy updates overnight or during maintenance periods), enforcing update deadlines (devices must update within X days of release), supporting rollback or deferral for updates that cause issues, and reporting on patch compliance (which devices are up to date, which are not).
Unpatched devices are the most common entry point for security incidents. Relying on end users to install updates voluntarily does not work. MDM patching should be automated, scheduled, and auditable.
10. Kiosk and Single-App Mode
MDM should be able to lock a device into a single application (single-app mode) or a curated set of applications (multi-app kiosk mode). This capability serves retail POS terminals, patient check-in tablets, digital signage displays, warehouse scanners, and any scenario where the device serves a single purpose, and the user should not be able to exit that purpose.
Kiosk mode on Android uses COSU (Corporate Owned, Single Use) configuration. On iOS, it uses Single App Mode or Autonomous Single App Mode. On Windows, it uses Assigned Access. The MDM should support all three platforms and allow IT to configure the kiosk experience — including custom branding, home screen layout, and navigation restrictions — from the central console.
11. Content Filtering and Data Loss Prevention
MDM should be able to control what content devices can access and how data flows between applications. Content filtering blocks access to unauthorized websites (by URL, category, or custom blocklist) and prevents employees from browsing malicious or non-productive sites on managed devices. Data loss prevention (DLP) controls restrict copy-paste between corporate and personal apps, disable screen capture in sensitive contexts, block USB data transfer, and prevent file sharing through unapproved channels.
In regulated industries — healthcare (HIPAA), finance (PCI-DSS), government (CJIS) — DLP controls are mandatory. They are audit requirements.
12. Geofencing and Location-Based Policies
MDM should be able to define geographic boundaries (geofences) and trigger device actions based on whether the device is inside or outside those boundaries. Use cases include locking a device when it leaves a campus or job site, automatically connecting to corporate VPN when the device enters the office, alerting IT when a high-value asset moves outside an authorized zone, and restricting app access based on location (no camera app in classified areas, no personal browsing on the factory floor).
Geofencing requires GPS or network-based location tracking with configurable reporting intervals. The MDM should track location history and generate movement reports for asset recovery and compliance purposes.
What CJIS Requires from Mobile Device Management
The CJIS Security Policy governs how law enforcement agencies and their contractors handle Criminal Justice Information (CJI). Any mobile device that accesses CJI must be managed by an MDM solution that meets specific requirements. The table below maps each CJIS requirement to the checklist capability that addresses it.
| CJIS Requirement | What MDM Must Do | CJIS Policy Section |
|---|---|---|
| Advanced authentication | Enforce multi-factor authentication (MFA) on every device accessing criminal justice information | 5.6.2.2 |
| Encryption at rest | Enforce full-disk encryption on all devices that store CJI locally | 5.10.1.2 |
| Encryption in transit | Push VPN profiles that encrypt all CJI transmissions between device and server | 5.10.1.3 |
| Audit logging | Log all CJI access events centrally with admin identity, timestamp, and action taken | 5.4.1 |
| Session management | Auto-lock devices after inactivity and terminate idle sessions within policy-defined timeouts | 5.5.5 |
| Access control | Restrict MDM admin functions and CJI access through role-based access control (RBAC) | 5.5.2 |
| Media protection | Execute remote wipe — selective or full — on lost, stolen, or compromised devices | 5.8 |
| Physical protection | Track device location via GPS and geofencing to monitor CJI asset movement | 5.9 |
| Patch management | Automate OS and application patching within CJIS-defined remediation timelines | 5.10.4.4 |
Organizations subject to CJIS should verify that their MDM vendor offers pre-built CJIS compliance templates that enforce these requirements automatically — rather than requiring manual policy configuration. Bento MDM includes CJIS compliance templates that map directly to the policy references above and can be applied fleet-wide from the admin console.
How to Evaluate MDM Capabilities Across Vendors
Having the capabilities on a feature list is different from having them work well in production. When comparing MDM vendors, use these evaluation criteria to separate marketing claims from operational reality:
- Are all 12 capabilities included at the base price? Some vendors include enrollment and basic policies at the entry tier but gate remote control, compliance templates, geofencing, and kiosk mode behind enterprise pricing. Ask specifically which capabilities require an upgrade.
- Do capabilities work equally across all platforms? A vendor may support Android kiosk mode but not iOS Single App Mode, or offer geofencing on mobile but not on laptops. Verify each capability on every OS in your fleet.
- Can the vendor demonstrate each capability in a trial? Request a free trial or guided demo that covers your highest-priority capabilities. If the vendor resists demonstrating a specific feature, it may not work as described.
- Does the vendor offer pre-built compliance templates? Building security policies from scratch is error-prone and time-consuming. Vendors that provide CIS Benchmark, NIST, and CJIS templates save weeks of configuration work and reduce compliance risk.
- Does the solution work in offline or disconnected environments? Most MDM solutions require continuous internet connectivity. If your fleet operates in locations with limited or no connectivity, verify that policies enforce offline and that management commands can queue until reconnection.
- What is the vendor’s approach to device ownership models? Your organization likely manages a mix of corporate-owned and employee-owned (BYOD) devices. Verify that the MDM supports both ownership models with appropriate data separation, privacy controls, and enrollment paths.
Bento MDM includes all 12 capabilities at every pricing tier, starting at $1/device — no enterprise gate, no per-feature add-ons. Cross-platform support covers Android, iOS, Windows, macOS, and Linux. Pre-built compliance templates for CIS, NIST, and CJIS are included. And Offline QR Commands — exclusive to Bento — enable management in environments where no other MDM solution can operate.
Frequently Asked Questions
What should mobile device management be able to do?
Mobile device management should be able to enroll devices at scale (zero-touch), enforce security policies (encryption, passcodes, VPN), distribute and manage applications, monitor device health and compliance, execute remote actions (lock, wipe, restart, view), support BYOD data separation, maintain audit trails, integrate with identity providers, automate patching, support kiosk mode, enforce content filtering and DLP controls, and provide geofencing and location-based policies. These 12 capabilities represent the minimum viable feature set for enterprise MDM.
What MDM capabilities does CJIS require?
CJIS requires advanced authentication (MFA minimum), encryption at rest and in transit, centralized audit logging of all CJI access, session timeouts, role-based access control, media protection (remote wipe), physical protection (device tracking), and timely patch management. These requirements map directly to MDM capabilities 2, 5, 7, 8, 9, and 12 in the checklist above.
How many capabilities should an MDM solution include?
An enterprise-grade MDM solution should include all 12 core capabilities as a baseline. Differentiation between vendors comes from deployment flexibility (cloud, on-premises, hybrid), pricing models (per-device vs per-user, feature gating vs all-inclusive), platform coverage depth, and unique capabilities such as offline device management.
What is the difference between MDM features and MDM capabilities?
Features are specific functions within the software — a button, a configuration screen, a report type. Capabilities are what the system can accomplish across those features — the ability to enroll devices at scale, enforce encryption, and wipe a device remotely. Capabilities matter for procurement and requirements documents. Features matter for implementation and daily operations.
Which MDM capabilities matter most for BYOD?
For BYOD programs, four capabilities are critical: data separation (work profiles and containerization to isolate corporate from personal data), per-app VPN (encrypting only corporate app traffic without routing personal browsing through the VPN), selective wipe (removing corporate data on offboarding without touching personal content), and identity provider integration (ensuring access is tied to the employee’s organizational account, not the device itself).
Related Articles

