MDM Best Practices — A Guide for IT Teams Managing Device Fleets
MDM best practices determine whether your deployment runs smoothly at scale or creates friction that drives users and admins to workarounds. A well-configured MDM platform is invisible to end users and effortless for IT. A poorly configured one generates support tickets, enrollment failures, and compliance gaps that consume more time than the software saves.
The 10 practices below are ordered by deployment lifecycle — from pre-deployment decisions through ongoing operations. Each practice includes what to do, why it matters, and the common mistake it prevents. If you are deploying MDM solutions for the first time, follow them in sequence. If you are optimizing an existing deployment, use them as an audit checklist.
10 Best Practices for Mobile Device Management
1. Define Your Device Policy Before Choosing MDM Software
What to do: Document which platforms you manage (Android, iOS, Windows, macOS, Linux), which ownership models you support (BYOD, COPE, CYOD), what compliance frameworks apply (HIPAA, CJIS, NIST, CIS), and what acceptable use looks like — before evaluating vendors. The policy defines requirements. The MDM software fulfills them.
Why it matters: The policy drives tool selection, not the reverse. Choosing software first leads to retroactive policy-making — you discover gaps after deployment when it costs the most to fix them. An MDM that doesn’t support your BYOD model or your compliance framework is a tool you will eventually replace.
Common mistake: Buying MDM based on a vendor demo, then realizing it doesn’t support on-premise deployment, Linux endpoints, or CJIS compliance. The demo looked good. The deployment failed at the policy layer.
For the policy document itself, see MDM Policy Template.
2. Use Zero-Touch Enrollment for Every New Device
What to do: Configure Android Automatic Enrollment, Apple Automated Device Enrollment (ADE), and Windows Autopilot as the default enrollment path for every new device. Devices should configure themselves on first boot — pulling policies, apps, and security settings from the MDM server without IT physically touching the hardware.
Why it matters: Manual enrollment does not scale. One technician can configure roughly five devices per hour by hand. Zero-touch enrolls thousands overnight. Every device that ships directly from the vendor to the employee and auto-configures on first boot is a device that never passes through IT’s hands, which eliminates the setup bottleneck entirely.
Common mistake: Using QR code or manual enrollment as a “temporary” solution and never migrating to zero-touch. Temporary becomes permanent. Six months later, IT is still hand-configuring every new phone.
3. Separate Corporate and Personal Data on Every BYOD Device
What to do: Deploy work profiles (Android) or managed app configurations (iOS) on every employee-owned device. Corporate apps, email, and data live inside a managed container. Personal apps, photos, and messages stay outside it. IT controls the container. The employee controls everything else.
Why it matters: Employees who believe IT can see their personal data will resist enrollment, unenroll their devices, or stop using their phones for work entirely. Work profiles solve this: IT manages corporate data without accessing personal content. The employee keeps their privacy. The organization keeps its security. Both sides get what they need.
Common mistake: Applying the same full-device MDM profile to BYOD devices and corporate-owned devices. On a corporate device, full management is expected. On a personal phone, it creates resentment, privacy complaints, and in EU jurisdictions, potential GDPR violations. BYOD requires app-level control, not device-level control.
4. Automate Patching — Do Not Rely on End Users
What to do: Configure MDM to push OS and application updates automatically on a schedule you control. Set enforcement deadlines — devices must update within a defined window after an update is released. Include rollback capability so you can revert an update that causes compatibility issues.
Why it matters: Unpatched devices are the most common entry point for security incidents. End users postpone updates indefinitely — the notification appears, they tap “Later,” and the device stays vulnerable for weeks. Automated patching removes the user from the equation. The MDM pushes the update. The device installs it. The compliance dashboard confirms it.
Common mistake: Setting the patch policy to “notify user” instead of “enforce.” Users dismiss the notification. Devices stay unpatched for months. The compliance report shows 40% of the fleet running an OS version two releases behind.
5. Use Compliance Templates — Do Not Build Security Policies from Scratch
What to do: Apply pre-built compliance templates for CIS Benchmarks, NIST frameworks, CJIS Security Policy, and HIPAA requirements as your security baseline. Customize from the template — adjust settings for your environment, add organization-specific rules — but start from a validated framework, not a blank configuration.
Why it matters: Building security policies from scratch is error-prone and time-consuming. A manual policy misses edge cases that compliance frameworks have already accounted for. Templates encode best practices from the framework itself — they have been tested against audit requirements and refined across thousands of deployments. Starting from a template saves weeks and reduces the risk of compliance gaps.
Common mistake: Spending three weeks building custom security policies that cover 70% of the compliance framework, then discovering the missing 30% during an audit. A template would have covered 95% on day one.
Bento MDM includes pre-built compliance templates for CIS, NIST, and CJIS at every pricing tier — no enterprise upgrade required to access compliance baselines.
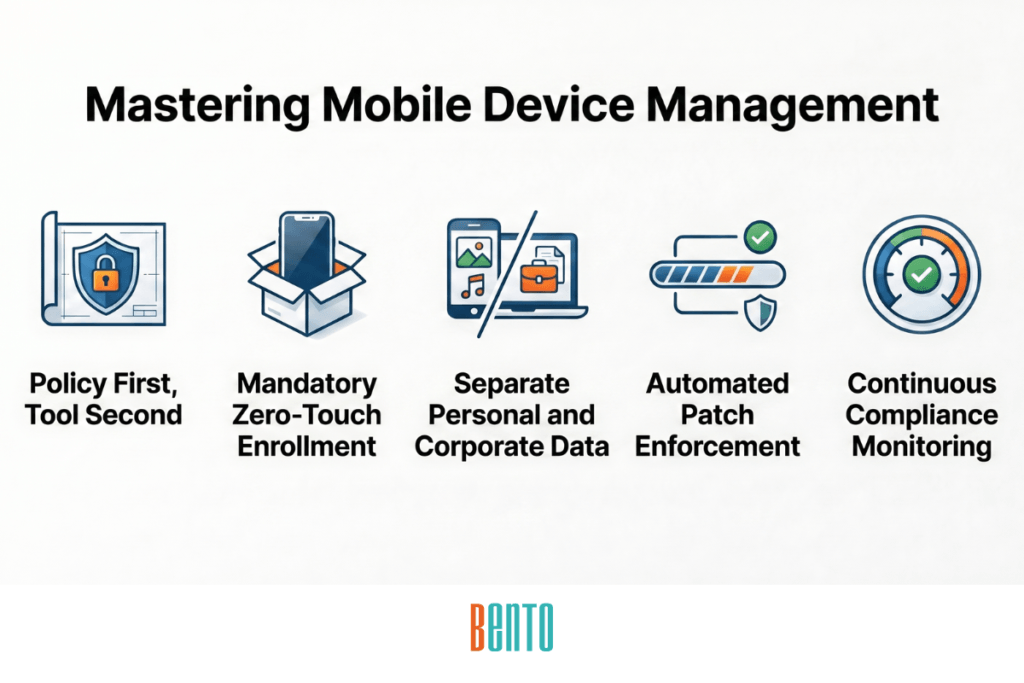
6. Monitor Device Compliance Continuously, Not on a Schedule
What to do: Configure real-time compliance monitoring with automated alerts. Your MDM dashboard should continuously show compliance status for each device, policy, and device group. When a device becomes non-compliant (user disables passcode, OS falls behind, device is jailbroken), the MDM should alert IT immediately and, optionally, trigger automated remediation.
Why it matters: Scheduled compliance checks — weekly reports, monthly audits — leave gaps. A device can be non-compliant for days or weeks before IT notices. In that window, corporate data on the device is unprotected. Real-time device monitoring closes the gap: the moment a device drops below the compliance baseline, IT knows and can respond.
Common mistake: Running compliance reports manually once a month, presenting them to leadership as “our compliance posture,” and treating them as sufficient audit evidence. The report shows a snapshot of one day. The other 29 days are unmonitored.
7. Restrict Admin Access with Role-Based Access Control
What to do: Configure RBAC so every MDM administrator sees and controls only what their role requires. Define separate roles: global admin (full access), device admin (enrollment and policies), app admin (application management only), and read-only auditor (view dashboards and reports, change nothing). Log every admin action in the audit trail.
Why it matters: A single shared admin account creates accountability gaps. When something goes wrong — a policy change breaks connectivity, a wipe command hits the wrong device group — nobody knows who did it. RBAC limits the blast radius of mistakes: a device admin cannot modify compliance templates, and an app admin cannot trigger remote wipes. Every action is logged against a named user.
Common mistake: Giving every IT team member full global admin access because “it’s easier than setting up roles.” It is easier — until someone accidentally pushes a factory reset to a production device group. RBAC prevents this by design.
8. Test Policy Changes on a Pilot Group Before Fleet-Wide Rollout
What to do: Create a dedicated test device group containing 5–10 devices across the platforms you manage. Push every new configuration, policy change, and app update to this pilot group first. Monitor for 24–48 hours. Verify that nothing breaks — connectivity, app functionality, user experience. Only then deploy fleet-wide.
Why it matters: An untested policy change that bricks 500 devices is a business interruption. The same change that bricks 5 pilot devices is a learning experience caught before impact. Pilot testing is the difference between a controlled rollout and an incident response.
Common mistake: Pushing a new Wi-Fi profile to the entire fleet without testing. The profile has a certificate error. One thousand devices lose connectivity simultaneously. IT spends the next 48 hours re-enrolling devices manually — because the broken profile prevents OTA remediation.
9. Document Your MDM Policy and Train Users at Onboarding
What to do: Write a plain-language device policy that covers acceptable use, BYOD enrollment expectations, what IT can and cannot see on enrolled devices, what happens if a device is lost or stolen, and how employees can get support. Include this document in every new-hire onboarding packet. Make it accessible on your intranet.
Why it matters: A policy that exists only in the MDM console is invisible to the people it affects. Users who do not understand the policy resist enrollment (“IT can see my photos”), misuse devices (installing unauthorized apps), and create support tickets that documentation would prevent (“Why can’t I access this website?”). A visible, readable policy sets expectations before friction occurs.
Common mistake: Deploying MDM with no user-facing documentation. Employees discover restrictions when they hit them — a blocked website, a mandatory passcode, a disabled camera — and react with frustration and helpdesk calls. Documentation prevents surprise. Surprise generates resistance.
For a ready-to-use template with all 10 sections, see MDM Policy Template.
10. Review and Update Policies Quarterly
What to do: Schedule a quarterly review of MDM policies, enrolled device inventory, compliance posture, patching status, and admin access roles. Check whether new OS versions require policy updates, whether compliance frameworks have issued revisions, whether the fleet composition has shifted (new device types, new ownership models), and whether any policies are creating unnecessary friction.
Why it matters: Device threats, compliance requirements, and organizational needs evolve. A policy written 18 months ago for a 200-device fleet running Android 13 may not fit a 2,000-device fleet running Android 15 with new BYOD users. Quarterly reviews catch drift before it becomes a gap — and they give IT a structured opportunity to remove outdated policies that no longer serve a purpose.
Common mistake: “Set and forget.” MDM is deployed, policies are configured, and nobody revisits them for a year. The fleet grows 5x. Three new OS versions ship. Two compliance frameworks update their requirements. The MDM configuration is now 12 months out of date — and the compliance report from last week shows a snapshot of policies that no longer reflect reality.
How to Prioritize These Practices for a New MDM Deployment
If you are deploying MDM for the first time, implementing all 10 practices simultaneously is overwhelming. The phased approach below sequences them by dependency — each phase builds on the previous one.
Phase 1 — Foundation (Week 1–2): Practices 1 and 2
Define your device policy and configure zero-touch enrollment. These two decisions shape everything that follows. The policy determines what you need from MDM. Zero-touch enrollment determines how devices enter the system. Get both right before configuring a single security policy.
Phase 2 — Security Baseline (Week 3–4): Practices 3, 4, and 5
Configure BYOD data separation, enable automated patching, and apply compliance templates. These three practices establish the security baseline that protects corporate data from day one. Without them, devices are enrolled but unprotected.
Phase 3 — Operational Maturity (Month 2): Practices 6, 7, and 8
Turn on real-time compliance monitoring, configure RBAC for the admin team, and create a pilot group for testing future changes. These practices prevent the operational errors that grow with fleet size. They are less urgent than the security baseline, but critical before the fleet scales.
Phase 4 — Sustainability (Month 3 and ongoing): Practices 9 and 10
Document the policy, train users, and establish the quarterly review cadence. These practices prevent drift. They are the difference between an MDM deployment that works for a year and one that works for five.
Bento MDM supports this phased rollout from a single console. Zero-touch enrollment, compliance templates, RBAC, real-time monitoring, and automated patching are included at $1/device from day one — nothing is gated behind an enterprise tier or a Phase 3 upgrade. You activate MDM capabilities as your deployment matures, not as your budget grows.
Frequently Asked Questions
What are the most important MDM best practices?
The three most impactful practices are: define your device policy before choosing software (to prevent misalignment between requirements and capabilities), use zero-touch enrollment for every new device (to eliminate the setup bottleneck), and automate patching (to close the most common security gap). These three practices alone prevent the majority of MDM deployment failures.
How often should MDM policies be reviewed?
Quarterly. Device threats, OS releases, and compliance framework updates occur throughout the year. A quarterly review catches policy drift before it creates compliance gaps. Additionally, review policies immediately after any major change — a new OS release, a compliance framework revision, a significant fleet expansion, or a shift in ownership model (adding BYOD to a previously corporate-only fleet).
What is the first thing to do when deploying MDM?
Define your device policy. Before evaluating vendors, document which platforms you manage, which ownership models you support, what compliance frameworks apply, and what your acceptable use rules look like. The policy drives every subsequent decision — vendor selection, enrollment configuration, security settings, and user training. Bento MDM’s setup wizard walks new deployments through policy configuration and zero-touch enrollment setup in under 30 minutes.
Should MDM policies be different for BYOD and corporate-owned devices?
Yes. Corporate-owned devices should use full device enrollment with device-level security policies — encryption enforcement, passcode requirements, remote wipe, and geofencing. BYOD devices should use work profiles or MAM-only enrollment with app-level controls — corporate data containerization, per-app VPN, selective app wipe. Applying the same full-device profile to both devices raises privacy concerns on BYOD devices and may violate regulations such as GDPR. For a detailed comparison, see BYOD vs COPE vs CYOD.
What is an MDM strategy roadmap?
An MDM strategy roadmap is a phased plan for deploying and maturing your mobile device management program. It sequences decisions and configurations by dependency: policy definition first, then enrollment, then security baseline, then operational controls, then documentation and review cadence. The phased rollout plan in this post follows this roadmap structure — four phases from foundation through sustainability, deployable over 8–12 weeks.
Related Articles