How to Plan Your MDM Implementation — From Evaluation to Scale
Mobile device management implementation follows six stages: evaluate and choose a solution, deploy and enroll devices, configure security and applications, monitor and manage the fleet, support and troubleshoot remotely, and scale as the organization grows. Each stage builds on the previous one. Skipping stages creates gaps that surface later as compliance failures, enrollment friction, or support overhead.
Most MDM implementation failures happen in Stage 1 (choosing the wrong vendor for your requirements) or Stage 3 (deploying incomplete security configurations). The technology itself rarely fails. The planning around it does.
This guide walks through each stage, including specific deliverables, the MDM solution features that activate at each phase, a timeline estimate, and common failure points to avoid. Use it as an implementation project plan or as an audit framework for an existing deployment.
The 6 Stages of MDM Implementation
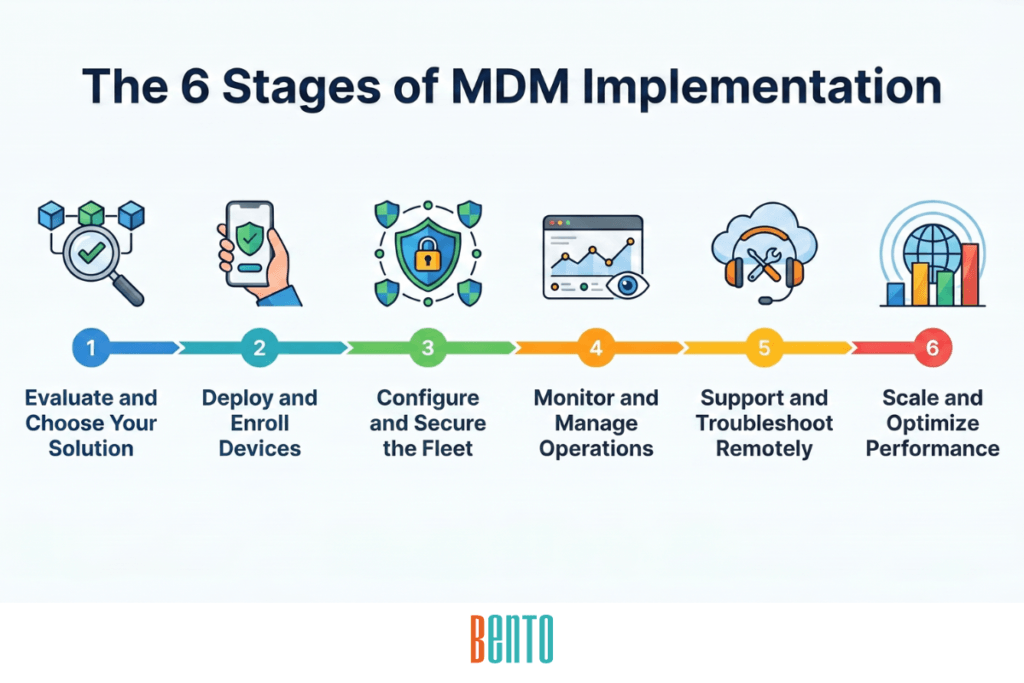
Stage 1 — Evaluate and Choose (Week 1–2)
Stage 1 is where IT assesses MDM requirements and selects a solution. This stage produces two deliverables: a device policy document and a vendor decision.
Device inventory: List every platform in your fleet (Android, iOS, Windows, macOS, Linux), every device type (smartphones, tablets, laptops, ruggedized, kiosks), and every ownership model you support (BYOD, COPE, CYOD). This inventory defines the scope of your MDM deployment.
Policy requirements: Document which compliance frameworks apply (HIPAA, CJIS, NIST, CIS, PCI-DSS), what acceptable use looks like, what happens when a device is lost or compromised, and how BYOD privacy is handled. The policy document is the first deliverable—it defines what you need before you evaluate the vendors’ offerings.
Deployment model: Decide whether you need cloud MDM, on-premise MDM, SaaS, or a hybrid model. This decision is driven by data sovereignty requirements, IT infrastructure resources, and compliance mandates. Government and defense organizations typically require on-premises. Most others start with cloud or SaaS.
Vendor evaluation: Test shortlisted vendors against the 12-capability checklist. Verify that the solution supports all platforms in your inventory, all ownership models in your policy, and all compliance frameworks you need. Request a free trial — demos show features; trials reveal gaps.
Bento MDM offers all three deployment models — cloud, on-premise, and SaaS — from a single console at $1/device, with all 12 capabilities included at every tier. This simplifies the vendor evaluation because there is no feature-gating discovery during the trial.
Common failure point: Choosing MDM based on a vendor demo without testing it against your policy requirements. The demo shows what the software can do in ideal conditions. Your policy defines what the software must do under your conditions. They are not the same thing. Always run a trial on your actual device types, enrollment methods, and compliance templates before committing.
For the policy document template, see MDM Policy Template.
Stage 2 — Deploy and Enroll (Week 2–3)
Stage 2 is where devices join the MDM platform. The goal is to enroll every device in the fleet through the fastest, most scalable method available — without IT physically touching hardware.
Zero-touch enrollment: Configure Android Zero-Touch Enrollment, Apple Automated Device Enrollment (ADE), and Windows Autopilot as the default enrollment path for corporate-owned devices. Devices ship from the vendor, power on, connect to Wi-Fi, and automatically pull their MDM profile. No IT intervention required.
BYOD enrollment: Configure QR code or enrollment link for employee-owned devices. When the employee scans a QR code or taps a link, the work profile installs, and corporate apps deploy within the managed container. Personal apps stay untouched.
Pilot group: Enroll 5–10 devices across your supported platforms into a test group before fleet-wide rollout. Verify that enrollment completes successfully, that connectivity profiles push correctly, and that the device experience matches expectations. Only after the pilot group is verified do you proceed to enroll the full fleet.
Connectivity and branding: Push APN configurations, Wi-Fi profiles, and VPN settings to enrolled devices. Apply custom branding (company logo, wallpaper, support contact information), so employees recognize the device as managed.
Common failure point: Enrolling the entire fleet on day one without a pilot group. If the enrollment profile contains a certificate error, a misconfigured Wi-Fi setting, or an incompatible policy, the error occurs on every device simultaneously. A pilot group catches the error on 5 devices instead of 500 — and the fix is a configuration change, not an incident response.
Stage 3 — Configure and Secure (Week 3–4)
Stage 3 deploys the security baseline across the enrolled fleet. This is the stage where most implementation gaps originate — not because the MDM lacks features, but because IT configures an incomplete subset and moves on.
Compliance templates: Apply pre-built security baselines for your applicable frameworks — CIS Benchmarks, NIST, CJIS, HIPAA. Start with the template and customize it, rather than building policies from scratch. Templates cover 90% of requirements on day one.
Passcode and encryption: Enforce passcode complexity requirements and full-disk encryption on every enrolled device. These two controls are non-negotiable—they are the baseline every compliance framework requires.
Application deployment: Push enterprise apps via silent install or through the Enterprise App Store. Configure managed app settings (server URLs, authentication tokens, per-app VPN) so apps work immediately without user configuration.
Access controls: Configure MFA and SSO for admin and user authentication. Set up RBAC for the admin team with separated roles: global admin, device admin, app admin, and read-only auditor. Every admin action from this point forward is logged against a named user.
BYOD and kiosk configuration: Configure work profiles for BYOD devices to isolate corporate data. Configure kiosk mode (COSU) for single-purpose devices — POS terminals, patient check-in tablets, warehouse scanners. Enable content filtering for web access control. Set scheduled configurations for deployments that should run outside business hours.
Common failure point: Configuring security policies without testing them on the pilot group first. A passcode policy that is too aggressive locks users out of their devices. A VPN profile with a wrong certificate breaks connectivity fleet-wide. A content filtering rule that blocks a critical internal URL prevents employees from doing their jobs. Test every configuration on the pilot group. Wait 24–48 hours. Verify nothing breaks. Then deploy fleet-wide.
Stage 4 — Monitor and Manage (Month 2, Ongoing)
Stage 4 transitions MDM from a deployment project to an operational system. The fleet is enrolled and secured. Now IT needs continuous visibility.
Compliance monitoring: Configure real-time compliance dashboards that display device status per policy and per device group as a part of device monitoring. Set automated alerts for non-compliant devices — a disabled passcode, an outdated OS, a jailbroken device. Non-compliance should trigger an immediate notification, not a weekly report.
Inventory and search: Verify that the device inventory search works across the entire fleet. IT should be able to search by device name, user, OS version, compliance status, enrollment date, and device group. This becomes the daily operational tool for fleet management.
Automated patching: Configure OS and app updates to push automatically on a schedule you control. Set enforcement deadlines so devices that defer updates are forced to install within a defined window. Enable rollback capability for updates that cause issues.
Location and communication: Activate geofencing and GPS tracking for asset monitoring. Test broadcast messaging for fleet-wide communications — announcements, maintenance windows, emergency alerts. Establish an audit log export schedule for compliance records.
Common failure point: Treating monitoring as a monthly reporting task instead of a real-time operational system. A device that goes non-compliant on Tuesday should trigger an alert on Tuesday. If the next compliance report runs on Friday, that device will have been unprotected for 3 days. Real-time monitoring closes the gap.
Stage 5 — Support and Troubleshoot (Month 2, Ongoing)
Stage 5 establishes the remote support infrastructure that eliminates most on-site visits. IT resolves device issues from the console instead of dispatching technicians.
Remote view and control: Test remote view and control on each supported platform. IT should be able to see the device screen live and interact with it — navigating menus, adjusting settings, diagnosing issues — without the employee describing the problem over the phone.
Just-in-Time access: Configure temporary elevated permissions for troubleshooting sessions. A support technician gets elevated access for 30 minutes to resolve an issue, then the access expires automatically. This prevents permanent admin access from persisting on devices after support is complete.
Offline device management: Bento MDM’s Offline QR Commands let IT push policies and execute fixes on devices with no internet connectivity. Test this capability for field devices, warehouse endpoints, and any device that operates in environments with unreliable connectivity. The QR code is generated in the console, the device scans it locally, and the command executes without a network connection.
Incident response: Document the remote wipe and lock procedure. Define the threshold: device reported lost for more than 24 hours triggers remote lock. Device confirmed to be stolen or compromised triggers a remote wipe (selective for BYOD, full factory reset for corporate-owned). Verify that factory reset protection prevents reactivation without managed credentials.
Common failure point: Having remote wipe capability but no documented procedure for when to use it. A panicked admin who wipes a device reported “lost” — when the employee left it in their car — unnecessarily destroys data. The procedure prevents panic-driven decisions.
Stage 6 — Scale and Optimize (Month 3+, Ongoing)
Stage 6 runs for as long as the fleet grows. The MDM platform is operational, security is enforced, monitoring is active, and support workflows are established. Now the question is: does this scale without proportionally scaling IT headcount?
Fleet growth: Add new devices using the same zero-touch enrollment flow established in Stage 2. A fleet that grows from 200 to 2,000 devices should follow the same enrollment, configuration, and monitoring process—not a new one designed for scale. If zero-touch enrollment is the default, adding 100 devices takes the same IT effort as adding 10.
Shared device management: Configure Shared Device Mode for organizations with shift workers (healthcare, logistics, retail). Multiple users share the same tablet with isolated sessions — each user logs in, gets their apps and data, and logs out without accessing the previous user’s session.
Cost optimization: Activate license metering to identify and reclaim unused software. Review per-device costs against fleet utilization. Identify devices that have not checked in for 30+ days — they may be lost, retired, or abandoned — and reclaim their licenses.
Quarterly review: Establish the quarterly policy review cadence from MDM best practices. Check whether new OS versions require policy updates, whether compliance frameworks have changed, whether the fleet composition has shifted (new device types, new BYOD users), and whether any policies create unnecessary friction. Every fleet expansion should trigger a policy review — a configuration that worked for 200 corporate-owned devices may not fit 2,000 devices that include BYOD, shared tablets, and kiosks.
Common failure point: Scaling the fleet without scaling the policies. The MDM platform handles 10x more devices. The policies were written for 1x. Security configurations, RBAC roles, compliance templates, and monitoring thresholds all need to be reviewed when the fleet composition changes materially.
MDM Implementation Timeline
The table below summarizes the timeline and key milestone for each implementation stage. Total time from evaluation to operational deployment is 4–6 weeks for most organizations. Scaling is continuous — Stage 6 runs for as long as the fleet grows.
| Stage | Timeline | Key Milestone |
|---|---|---|
| 1. Evaluate and Choose | Week 1–2 | Vendor selected and device policy document completed |
| 2. Deploy and Enroll | Week 2–3 | Pilot group enrolled successfully and zero-touch configured for fleet-wide deployment |
| 3. Configure and Secure | Week 3–4 | Security baseline deployed and verified across all enrolled devices |
| 4. Monitor and Manage | Month 2+ | Real-time compliance dashboards operational with automated alerts active |
| 5. Support and Troubleshoot | Month 2+ | Remote support workflows tested and incident response procedures documented |
| 6. Scale and Optimize | Month 3+ | Fleet growth runs on the same enrollment and policy framework established in Stages 1–3 |
Bento MDM’s setup wizard completes the Stage 1 evaluation and Stage 2 enrollment configuration in under 30 minutes. The 4–6 week timeline accounts for policy decisions, pilot testing, and organizational readiness — not the software setup itself.
Cross-Stage Features — What Persists Across the Entire Implementation
Some MDM features are configured once and then operate continuously across multiple stages. Understanding these cross-stage connections prevents the “configure and forget” mistake where IT sets up a feature in Stage 3 and doesn’t revisit it when it becomes relevant again in Stage 5 or 6.
Zero-Touch Enrollment spans Stages 2 through 6. It is configured during deployment, but the same enrollment flow is reused every time a new device is added to the fleet — whether that is 10 devices in month one or 1,000 devices in year two.
Role-Based Access Control spans Stages 3 through 6. RBAC is configured during the security baseline stage and then governs every admin action in monitoring, support, and scaling. When new admins join the team, they receive a role — not a shared global-admin credential.
Compliance Templates span Stages 3 and 4. They are applied during configuration and then generate the compliance reports used during monitoring. If a compliance framework issues an update, the templates need to be updated in Stage 3, and the monitoring dashboards need to be refreshed in Stage 4.
Offline QR Commands span Stages 3 through 5. Policies configured in Stage 3 are enforced offline. Troubleshooting in Stage 5 works offline. This capability is unique to Bento MDM and becomes critical for any fleet that includes devices operating in disconnected environments.
BYOD Work Profiles span Stages 3 through 6. Work profiles are configured during the security baseline and then enforced continuously through monitoring, support, and scaling. When new BYOD users join the organization, they enroll in the same work profile configuration established in Stage 3.
Frequently Asked Questions
How long does MDM implementation take?
Most organizations complete the initial deployment (Stages 1–3) in 4–6 weeks. This includes vendor evaluation, policy documentation, enrollment configuration, pilot testing, and security baseline deployment. Stages 4–6 (monitoring, support, and scaling) are ongoing operations that continue for the life of the fleet. The software setup itself takes minutes to hours. The timeline is driven by organizational decisions — policy definition, compliance requirements, pilot testing — not by technical complexity.
What is the first step in MDM deployment?
Define your device policy before selecting a vendor. Document which platforms you manage, which ownership models you support, what compliance frameworks apply, and what acceptable use looks like. The policy determines your MDM requirements. The vendor evaluation tests whether each solution meets those requirements. Choosing software before defining the policy reverses the dependency and leads to retroactive policy-making.
Do I need to enroll all devices at once?
No. Start with a pilot group of 5–10 devices across your supported platforms. Verify that enrollment, policies, and connectivity work correctly on the pilot group before enrolling the full fleet. After the pilot is verified, enroll the remaining fleet in phases — by department, by location, or by device type. A phased rollout limits the blast radius of any configuration error.
What is an MDM implementation project plan?
An MDM implementation project plan is a staged roadmap that sequences the decisions, configurations, and milestones required to deploy and operate MDM. The 6-stage framework in this guide serves as a project plan: Stage 1 produces a policy document and vendor decision; Stage 2 produces enrolled devices; Stage 3 produces a security baseline; Stage 4 produces operational dashboards; Stage 5 produces support workflows; and Stage 6 produces a scalable growth process. Each stage has deliverables, timelines, and a success criterion.
Can I migrate from one MDM to another?
Yes, but it requires planning. MDM migration involves re-enrolling devices from the old platform to the new one, which typically means unenrolling from the old MDM, enrolling in the new MDM, and repushing policies and apps. For corporate-owned devices, zero-touch enrollment simplifies migration because devices can be reassigned to the new MDM server and re-enrolled on next boot. For BYOD devices, users need to install the new work profile. Plan for a parallel period where both MDM platforms run simultaneously during the transition.
Related Articles