Classroom Device Management - Managing Student and Staff Devices in K-12 and Higher Ed
Classroom device management is the process by which schools and higher education institutions enroll, configure, and secure the devices students and staff use every day. iPads in shared classroom carts, Chromebooks in 1:1 take-home programs, Windows laptops in computer labs, Android tablets at library checkout stations — every device that touches a learning environment falls under the classroom device management umbrella. Mobile Device Management (MDM) is the software layer that makes classroom device management work at scale: it enrolls devices, enforces CIPA-compliant content filtering, distributes educational apps, locks devices for standardized testing, and tracks every device from procurement through end-of-life refresh.
Education MDM differs from enterprise MDM in three ways. First, compliance is driven by CIPA and FERPA rather than HIPAA or SOC 2. Second, devices are frequently shared among students rather than assigned to a single user. Third, users — students — actively attempt to bypass restrictions, which means controls such as factory reset protection and device-level content filtering carry more weight than they do in corporate environments. Solutions like Bento MDM manage school device fleets for $1/device, with all features included — content filtering, kiosk mode, app management, and device tracking — and no enterprise-tier gating.
This guide covers CIPA compliance and content filtering, 1:1 and shared device programs, exam lockdown, app distribution, FERPA data protection, Chromebook management, and how MDM differs from classroom management software. For the foundational definition of MDM — what it is, how enrollment works, and what it manages — start with what mobile device management is and how it works.
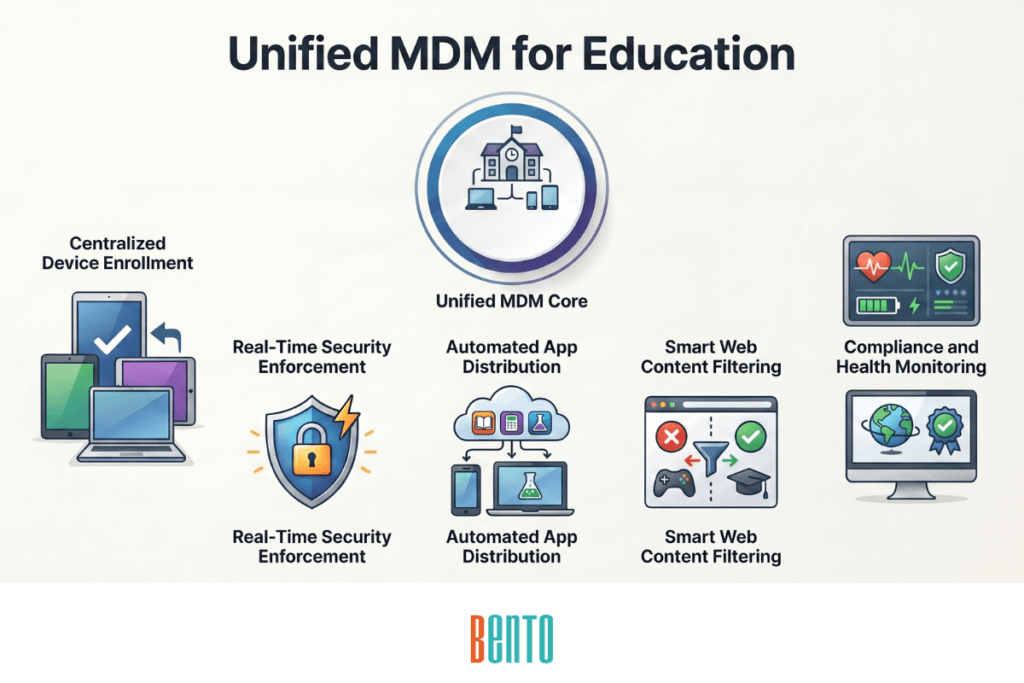
What MDM Does in Educational Environments
MDM for education enrolls, configures, and secures student and staff devices from one console. It silently pushes educational apps, enforces web content filtering that follows devices on- and off-campus, applies different access policies to student devices versus teacher devices, and provides IT with real-time visibility into device health, compliance status, and location across the district.
The capabilities MDM provides in education are the same 12 core capabilities every MDM solution must have: enrollment, security enforcement, app distribution, compliance monitoring, remote wipe, BYOD separation, audit logging, identity integration, patching, kiosk mode, content filtering, and geofencing. What changes in education are how those capabilities are configured: content filtering uses CIPA categories instead of corporate blocklists, kiosk mode locks devices for testing instead of retail POS, and shared device workflows reset between students instead of between shift workers.
CIPA Compliance and Content Filtering for School Devices
The Children’s Internet Protection Act (CIPA) is the compliance requirement that drives most school MDM deployments. Schools and libraries that receive E-Rate funding — the federal program that subsidizes internet and technology costs — must implement content filtering on every device that students use to access the internet. Without CIPA compliance, the district loses its E-Rate discount.
What CIPA Requires
CIPA mandates three categories of filtering on devices accessed by minors: obscene visual depictions, child sexual abuse material, and content harmful to minors. CIPA also requires the school to adopt and enforce an internet safety policy that addresses unauthorized access, unauthorized disclosure of personal information, and measures to restrict minors’ access to harmful materials. The filtering requirement applies to school-owned devices and to personal devices accessing the school’s network.
How MDM Enforces CIPA Content Filtering
MDM pushes URL- and category-filtering policies directly to managed devices. The filter runs on the device itself — not on the school’s network. This distinction matters because network-based content filters (DNS filtering, proxy servers, firewall rules) only work when the device is connected to the school’s network. When a student takes a 1:1 iPad home and connects to their family’s Wi-Fi, the school’s network filter is bypassed. MDM device-level filtering follows the device everywhere — on school Wi-Fi, on home Wi-Fi, on cellular, on a public hotspot at the library.
Bento MDM enforces CIPA-compliant content filtering across Android, iOS, and Windows devices from one console. Category-based blocking covers the CIPA-mandated categories as well as additional categories that districts commonly block: social media, gaming, streaming, gambling, and violence. URL-level exceptions let IT unblock specific educational resources within a blocked category. For the full technical breakdown of how MDM web filtering works, including allowlist and blocklist configuration, see MDM web content filtering.
Teacher vs Student Filtering Tiers
Students and teachers need different levels of web access on the same device models. Students receive strict CIPA filtering — social media blocked, streaming blocked, search restricted to safe mode. Teachers receive broader access to research databases, instructional video platforms like YouTube (with restricted mode enabled), and professional development sites that students cannot reach. MDM applies different content filtering policies per device group, so IT assigns student devices to the “Student” group and teacher devices to the “Staff” group, each with its own URL and category rules.
1:1 Device Programs — One Device Per Student
In a 1:1 program, every student receives a dedicated device — typically a Chromebook, iPad, or Windows laptop — for the school year. The device travels between school and home daily. MDM is the only way to manage a fleet of devices that spends half its time on networks IT does not control.
Zero-Touch Enrollment at Scale
District IT pre-registers device serial numbers with the MDM server. Devices ship from the manufacturer or distributor to the school or directly to the student’s home address. On first boot and Wi-Fi connection, each device automatically contacts the MDM server, downloads the MDM agent, applies the student policy profile, installs educational apps, and activates CIPA content filtering. A district deploying 5,000 iPads enrolls them the same way as 50 — no manual configuration, no USB cables, no app store browsing. The MDM implementation guide covers the zero-touch enrollment workflow for Android, iOS, and Windows in detail.
Off-Campus Device Management
1:1 take-home devices operate on student home networks — unmanaged Wi-Fi with no school firewall, no DNS filtering, and no network-level content controls. MDM enforces the same content filtering, security policies, and app restrictions off-campus as on-campus because enforcement occurs on the device, not on the network. Patch updates push over the home connection during off-hours. If a device is lost or stolen, IT can remotely lock or selectively wipe it from the console without requiring the student to return the device. For the complete framework on managing devices outside the corporate or school network, see MDM for remote and hybrid teams.
End-of-Year Device Refresh
At the end of the school year, IT remotely wipes returning devices and re-provisions them for the next student cohort. MDM tracks which devices have been returned, which are still outstanding, and which need hardware service based on battery health, screen condition reports, and age. Factory reset protection prevents students from wiping the device during the year and repurposing it as a personal device — even if they factory reset through the recovery menu, the device re-enrolls in the MDM on next boot.
Shared Device Carts — iPads and Tablets Across Classrooms
Not every school runs a 1:1 program. Many elementary schools and special programs use shared device carts — carts of 30 iPads or Android tablets that roll between classrooms. A second-grade class uses the cart during reading time; a fourth-grade class uses it during math. The devices must reset between sessions so no student sees another student’s data.
Shared iPad and Shared Android Tablet Workflows
On the Apple Shared iPad, each student logs in with a Managed Apple ID and gets their own data partition. When the student logs out, their data is cached but inaccessible to the next student. On Android, MDM’s shared device mode clears the user session and restores the baseline profile between students. No browsing history, no saved passwords, no cached app data carries over. The device is clean for every student.
Cart Tracking and Inventory
MDM inventories every device in every cart — serial number, battery level, last sync time, assigned app set, and compliance status. Teachers check out a cart and return it at the end of the period. MDM automatically flags a cart if it returns with fewer devices than it left with. Device inventory and management provides IT with a real-time count of every device in the district, without manual spreadsheets or barcode scanning.
Exam Lockdown — Kiosk Mode for Standardized Testing
MDM locks devices to a lockdown browser application for standardized testing using kiosk mode. On Android, COSU (Corporate Owned, Single Use) dedicated device mode replaces the home screen with the testing app. On iOS, Single App Mode restricts the device to the lockdown browser. On Windows, Assigned Access achieves the same restriction. During testing: no app switching, no screenshots, no notification access, no browser tabs, no copy-paste.
Schedule-based kiosk activation is critical for schools. The testing window opens at 8:00 AM and closes at 11:30 AM. MDM automatically activates kiosk mode at 8:00 AM and deactivates it at 11:30 AM, returning the device to its normal classroom configuration. The same device functions as a general learning tool before and after the exam period. No manual device-by-device lockdown required. For the full technical breakdown of single-app and multi-app kiosk mode across Android, iOS, and Windows, see MDM kiosk mode for single-app and multi-app lockdown.
App Distribution for Education
Schools distribute hundreds of educational apps across thousands of devices — reading apps for elementary, graphing calculators for high school, LMS clients for every grade, and specialized apps for special education. MDM handles app distribution silently, at scale, without student interaction.
Apple School Manager and Volume Purchase
Apple School Manager (ASM) integrates with MDM for device enrollment and volume app licensing. IT purchases app licenses in bulk through Apple School Manager, assigns them to devices or student groups, and MDM silently installs the apps. When the student completes the school year, the license is revoked and reassigned to the next cohort — the district buys licenses once and reuses them indefinitely. No app store browsing. No student-initiated downloads. No Apple ID required on managed devices.
Managed Google Play for Android and Chromebook
For Android tablets and Chromebooks, MDM distributes apps through managed Google Play. IT approves apps once and deploys them silently across every device in the assigned group. Private apps — district-developed tools, custom student portals, or locally built assessment apps — distribute through managed Google Play without public publishing. Bento MDM integrates with managed Google Play for silent app installation, version pinning, and managed app configurations that push server URLs and license keys directly into the app.
Windows App Deployment
For Windows laptops in computer labs and 1:1 programs, MDM pushes .msi and .msix packages or Microsoft Store apps. Version pinning ensures every student device runs the same application version — critical for instruction when the teacher’s screen must match the student’s. Application and software management covers the full app lifecycle: silent install, update, version lock, and remote uninstall.
FERPA and Student Data Protection
The Family Educational Rights and Privacy Act (FERPA) protects student education records. Any device that accesses student information systems — the SIS, the LMS gradebook, attendance records, and IEP documentation — must protect that data from unauthorized access. FERPA does not mandate specific technology, but the controls it requires map directly to MDM capabilities:
MDM enforces encryption on every device that accesses student records — data at rest and data in transit. MDM restricts which apps can access student data through managed app configurations and per-app VPN. MDM enforces screen lock timeouts on shared devices to prevent the next student from viewing the prior student’s records. MDM logs which devices accessed student information systems and when. MDM enables selective wipe when a device is lost or decommissioned, removing all cached student data without returning the device.
FERPA’s requirements parallel HIPAA’s Technical Safeguards in structure — both mandate access controls, encryption, and audit logging on devices that access protected records. The MDM for healthcare guide covers HIPAA-to-MDM mapping; the same mapping pattern applies to FERPA. For a broader view of how MDM satisfies compliance frameworks, the MDM capabilities checklist maps all 12 core capabilities to compliance requirements, including CJIS, HIPAA, and FERPA.
Chromebook Management in Education
Chromebooks are the most deployed device in U.S. K-12 education. Chrome OS devices are managed natively through Google Admin Console, which handles OS-level policies, user management, Chrome browser restrictions, and enrollment. Google Admin Console is the primary management tool for any Chromebook fleet.
MDM adds value when a district manages a mixed fleet — Chromebooks alongside iPads and Windows laptops. In a mixed-fleet environment, IT runs Google Admin Console for Chrome OS policies and a separate MDM console for iOS and Windows policies. This means two dashboards, two policy engines, and two compliance reports. MDM platforms that support Chromebook enrollment alongside other operating systems consolidate visibility: IT can see Chromebook compliance status, iPad patch levels, and Windows encryption status in a single dashboard, rather than three.
MDM also extends Chromebook management with capabilities beyond Google Admin Console’s native feature set: cross-platform content filtering (applying the same CIPA policy to Chromebooks, iPads, and Windows devices), unified device lifecycle tracking (warranty status, age, assignment history across all device types), and centralized app deployment reporting.
A district running an all-Chromebook fleet may not need MDM beyond Google Admin Console. A district running Chromebooks alongside iPads, Windows laptops, and Android tablets needs MDM to unify management across all platforms.
MDM vs Classroom Management Software
MDM and classroom management software are different tools that serve different purposes. The distinction matters because school IT teams frequently conflate them, and vendors in both categories use overlapping marketing language.
MDM manages the device. It handles enrollment, security policy enforcement, app distribution, content filtering, remote wipe, patching, and compliance monitoring. MDM runs continuously — 24 hours a day, 365 days a year — whether the device is in a classroom, at home, or powered off in a storage cart. MDM is an IT infrastructure. The MDM vs EMM vs UEM comparison explains how device management scope expands from mobile-only (MDM) through application management (EMM) to all endpoints (UEM).
Classroom management software manages the classroom session. Products like Securly Classroom, LightSpeed Classroom Management, and GoGuardian Teacher let the teacher see every student’s screen in real time, lock screens for attention, close distracting tabs, push URLs to all devices, and restrict browsing to specific sites during the lesson. Classroom management runs only during instruction — when the teacher activates a session, the controls engage; when the class ends, they release.
Most districts run both. MDM is the foundation layer — it ensures every device is enrolled, filtered, patched, and compliant before a student ever opens the device. Classroom management software sits on top — it gives teachers instructional control during class time. MDM without classroom management means IT manages devices, but teachers cannot control student screens during lessons. Classroom management without MDM means teachers can see screens during class, but IT has no way to enforce security policies, push patches, or wipe lost devices.
Frequently Asked Questions on Classroom Device Management
What does MDM mean in schools?
MDM in schools is Mobile Device Management — software that school IT teams use to enroll, configure, secure, and manage student and staff devices from one console. MDM handles content filtering, app distribution, kiosk mode for testing, device tracking, and remote wipe. In education, MDM refers specifically to mobile device management, not master data management.
How much does MDM for schools cost?
Pricing varies by vendor and fleet size. Bento MDM costs $1/device/month and includes all features — CIPA-compliant content filtering, kiosk mode for testing, app distribution, device tracking, and remote wipe. No features are gated behind enterprise tiers. Volume pricing is available for large districts. Some vendors offer free tiers for small deployments, but restrict content filtering or compliance reporting to paid plans.
Is MDM required for CIPA compliance?
CIPA requires “technology protection measures” that block access to visual depictions that are obscene or harmful to minors. CIPA does not mandate MDM by name. However, device-level content filtering — which MDM provides — is the only filtering approach that works both on-campus and off-campus. Network-based filters (DNS filtering, proxy servers) fail when 1:1 devices leave campus and connect to student home networks. Most districts use MDM alongside network filtering to achieve complete CIPA coverage on every device, everywhere.
What is the difference between MDM and classroom management software?
MDM manages the device enrollment, security policies, app distribution, content filtering, patching, and remote wiping. MDM runs continuously, whether the device is in a classroom or at home. Classroom management software manages the classroom session — the teacher views student screens, locks devices, closes tabs, and pushes links during instruction. Most districts run both: MDM as IT infrastructure and classroom management software as the teacher’s instructional control layer.
Can MDM manage Chromebooks?
Chrome OS devices are managed primarily through Google Admin Console, which handles OS-level policies, user management, and Chrome browser restrictions. MDM adds value when a district manages a mixed fleet — Chromebooks alongside iPads and Windows laptops. MDM provides cross-platform visibility, unified CIPA content filtering across all device types, and consolidated device lifecycle tracking in one dashboard. A district running only Chromebooks may not need MDM beyond Google Admin Console.
How does MDM manage take-home 1:1 devices?
MDM enforces the same security policies, CIPA content filtering, and app restrictions on take-home devices that it applies on campus. The MDM agent communicates with the server over the student’s home internet connection. Patches are pushed over the air during off-hours. Content filtering runs on the device, not on the network, so it works on any Wi-Fi connection. If a device is lost or stolen, IT can remotely lock or wipe it from the MDM console.
Does MDM protect student data under FERPA?
FERPA requires schools to protect student education records from unauthorized access. MDM enforces encryption, screen lock timeouts, access controls, and selective wipe on devices that access student information systems — all controls that support FERPA compliance. MDM also logs which devices accessed student data and when, providing the audit trail FERPA requires. MDM does not access student records itself — it secures the device that accesses them.
Related Articles