MDM Kiosk Mode — How to Lock Devices for Retail, Healthcare, and Field Service
MDM Kiosk mode is a Mobile Device Management capability that locks a device to a single application or a curated set of applications. The home screen, settings menu, notification shade, and navigation buttons are disabled or hidden. The end user interacts only with the approved app. When the app is closed or crashes, the device restarts the app automatically — never exposing the underlying operating system.
Any enrolled device — Android tablet, iPad, Windows laptop, ruggedized handheld — becomes a single-purpose tool when MDM applies a kiosk policy. The hardware stays the same. The software configuration makes it a kiosk. Retail POS terminals, hospital check-in tablets, digital signage displays, warehouse scanners, and classroom testing devices all use kiosk mode to restrict the devices to a single function.
This guide covers how kiosk mode works on each platform (Android, iOS, Windows), which industries use it and how, and what MDM capabilities are required to operate kiosk devices securely at scale.
What Is Kiosk Mode and How Does It Work?
Kiosk mode restricts a device to a specific application or set of applications defined by IT. The device boots directly into the approved app. The home screen is replaced. System settings are inaccessible. The status bar and navigation buttons are hidden or disabled. The user cannot install apps, browse the web, or access any function outside the kiosk experience.
Two kiosk variants exist. Single-app kiosk locks the device to one application — a POS terminal running only the payment app, a check-in tablet running only the registration app, a digital sign running only the signage player. A multi-app kiosk locks the device to a curated set of applications selected by IT — a field service device with a diagnostic app, a camera, a barcode scanner, and a reporting tool, but nothing else. Single-app is for public-facing and single-function devices. Multi-app is for worker devices that need multiple tools but no personal access.
How MDM Kiosk Mode Works on Each Platform
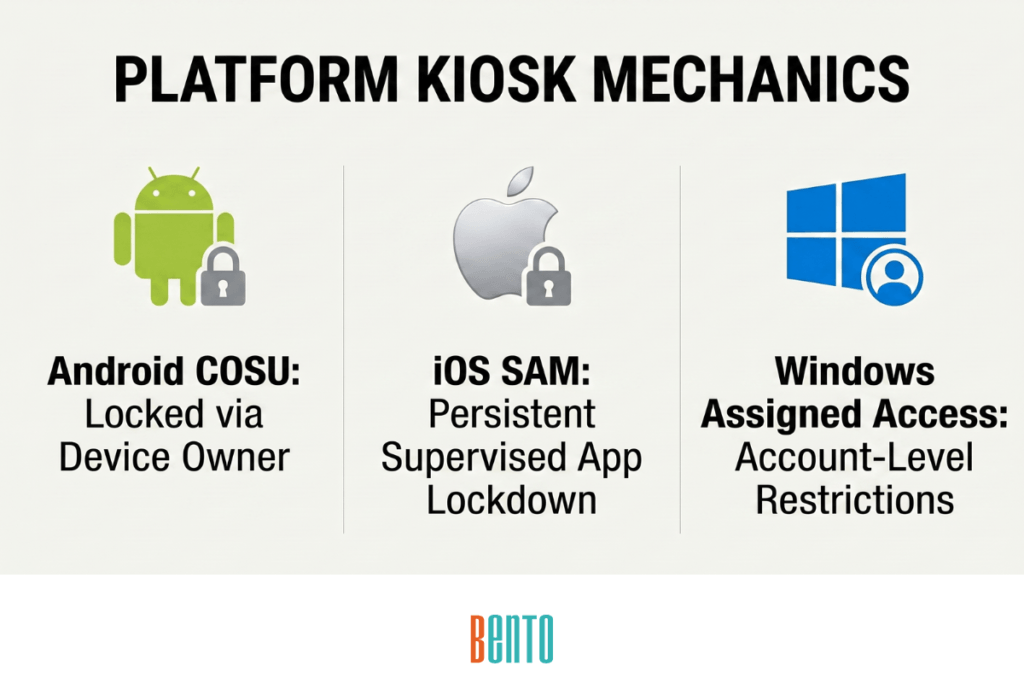
Android — COSU (Corporate Owned, Single Use) Mode
Android Enterprise provides a dedicated device mode, also called COSU (Corporate Owned, Single Use). MDM enrolls the device as a dedicated device and applies a lock task policy that pins one or more applications to the foreground. The home screen is replaced by the approved app. Navigation buttons are disabled. The notification shade is blocked. The user cannot access settings, install apps, or switch away from the kiosk experience.
Android COSU requires Android 6.0 or higher and requires the device to be enrolled via zero-touch enrollment or a QR code. The MDM must be configured as Device Owner — which means COSU enrollment must happen during device setup (first boot or factory reset), not after the device is already in use. Devices already configured with a personal Google account cannot be retroactively converted to COSU without a factory reset.
Bento MDM supports COSU mode on all Android 6.0+ devices, including Samsung, Zebra, Honeywell, and Lenovo. Enrollment via zero-touch or QR code configures the device as a dedicated kiosk automatically on first boot.
iOS / iPadOS — Single App Mode
iOS provides Single App Mode (SAM) through MDM supervision. MDM pushes an MDM profile that locks the device to a single application. The home button is disabled. Swipe gestures are blocked. Touch, motion, and volume button behavior can be restricted. The device boots into the locked app and stays there until the MDM profile is removed.
Single App Mode is different from Guided Access. SAM is MDM-managed, persistent, and survives restarts — when the device reboots, it automatically returns to the locked app. Guided Access is user-initiated, temporary, and requires a passcode to exit — a user can enable Guided Access on any app at any time, and anyone with the passcode can disable it. For kiosk deployments, Single App Mode is the correct approach because it is centrally managed by MDM and cannot be exited by the user.
iOS Single App Mode requires the device to be enrolled and supervised via Apple Automated Device Enrollment (ADE). Unsupervised devices — including manually enrolled or retail-purchased devices without ADE — cannot use SAM. Only Guided Access is available on unsupervised devices, which is insufficient for production kiosk deployments because users can exit it.
Windows — Assigned Access
Windows provides Assigned Access for kiosk configurations. Single-app mode locks the device to one UWP (Universal Windows Platform) application or a web app displayed in a kiosk browser. Multi-app mode presents a custom Start menu that shows only approved applications — the full Start menu, taskbar, and system settings are hidden.
Assigned Access is configured through MDM policy or Windows Configuration Designer. It applies at the user account level — a dedicated kiosk account is created with the Assigned Access restrictions, while an admin account retains full access for maintenance. Windows Assigned Access requires Windows 10 or 11 Pro, Enterprise, or Education. Windows Home does not support Assigned Access.
Industry Use Cases for Kiosk Mode
Retail — Point of Sale and Self-Checkout
Retail kiosk mode locks Android tablets and iPads to the POS application for checkout, payment processing, and inventory lookup. Self-checkout stations use single-app kiosk mode, so customers interact only with the checkout interface — they cannot navigate to settings, install apps, or access the browser. Product lookup kiosks on the sales floor display the product catalog in a single-app browser that points to the store’s website.
Retail kiosk configuration: single-app COSU (Android) or SAM (iOS), content filtering to block everything except the POS server URL, factory reset protection to prevent staff or customers from resetting the device, auto-restart on crash (the kiosk app relaunches within seconds if it fails), and custom branding with the store logo and product imagery.
Healthcare — Patient Check-In and Wayfinding
Healthcare kiosk mode locks tablets to patient check-in applications, wayfinding terminals, and patient education displays. Check-in kiosks collect insurance information, verify identity, and capture signatures — data that qualifies as ePHI under HIPAA. These devices require full-disk encryption and kiosk lockdown, as the data they collect is regulated by Healthcare MDM.
Healthcare kiosk configuration: single-app kiosk with auto-clear between patient sessions (no previous patient’s data persists), content filtering to block all browsing outside the check-in application, factory reset protection, and HIPAA-compliant encryption. Wayfinding kiosks that display maps and directories without collecting patient data have simpler requirements — single-app lockdown with content filtering is sufficient.
Digital Signage — Displays and Information Boards
Digital signage kiosk mode locks devices to a signage player application that runs content on a continuous loop — menu boards in restaurants, departure screens in airports, promotional displays in retail, event schedules in conference centers. No user interaction occurs. The device runs unattended 24/7.
Digital signage configuration: single-app kiosk running the signage player, content updates pushed OTA by MDM or the signage platform, automated patching scheduled during off-hours (a menu board that reboots for an update during lunch service is a problem), and remote view so IT can verify what the screen displays without visiting the physical location. MDM remote view is especially valuable for signage — a display showing an error message or a blank screen in a customer-facing location needs to be identified and fixed before an employee notices.
Field Service — Diagnostic and Data Collection Devices
Field service kiosk mode uses multi-app configuration to give technicians access to a curated set of tools: a diagnostic application, a camera for documenting work, a barcode scanner, and a reporting or ticketing app. The device has everything the technician needs — and nothing they do not. No social media, no games, no browser, no access to personal app stores.
Field kiosk configuration: multi-app COSU with the approved tool set, ruggedized device hardware (Zebra, Honeywell) for harsh environments, and offline management capability. Field devices operate in warehouses, construction sites, mines, agricultural properties, and remote service locations where cellular and Wi-Fi connectivity is unreliable or nonexistent. Bento MDM’s Offline QR Commands let IT push policy updates and configuration changes to field kiosks without a network connection — extending MDM management to locations where no other solution can operate.
Education — Testing and Student Devices
The education kiosk mode serves two scenarios. Standardized testing locks the device to a lockdown browser for the duration of the exam — students cannot switch apps, access notes, browse the web, or take screenshots. Student devices in general classroom use run a multi-app kiosk with only approved educational applications, content filtering that blocks non-educational websites, and restrictions on app installation.
Education kiosk configuration: schedule-based kiosk mode that activates during testing hours and deactivates for general use. MDM pushes the kiosk policy before the testing window and removes it after — the same device serves as a locked testing terminal during exams and a general classroom tool during instruction. Content filtering runs continuously regardless of kiosk state, blocking inappropriate content during both testing and general use.
MDM Capabilities Required for Kiosk Deployments
Kiosk mode locks the app. But a locked device still needs updates, security, monitoring, and troubleshooting. Deploying kiosk mode without the supporting MDM capabilities creates devices that are locked but unmanaged, which becomes a security and operational problem within months. These 6 capabilities must be present in kiosk mode for a secure, scalable deployment.
1. Kiosk lockdown (single-app or multi-app). The core capability — locking the device to the approved application or application set with home screen replacement, navigation suppression, and auto-restart on crash.
2. Factory reset protection. Prevents anyone from factory-resetting the device and removing the kiosk configuration. Without FRP, a retail employee who gets frustrated with the POS terminal can hold the power button, reset the device, and set it up as a personal tablet. FRP prevents the device from being reactivated after a reset without managed credentials.
3. Content filtering. Blocks network access to everything except the URLs and services the kiosk app needs. A patient check-in kiosk should connect only to the check-in server. A POS terminal should connect only to the payment processor. Content filtering prevents the device from reaching anything else — even if the kiosk app has a web view or embedded browser.
4. Automated OTA patching. Kiosk devices run unattended for months. They still need OS updates and app updates. MDM automatically pushes patches during off-hours, keeping the device up to date without manual intervention. Without automated patching, a kiosk running a 12-month-old OS with known vulnerabilities is an unpatched endpoint on your network.
5. Remote view and control. Kiosk devices are often in locations where IT cannot easily visit — a retail store across the state, a hospital lobby, a conference center. Remote view lets IT see exactly what the kiosk screen displays and interact with it remotely to diagnose issues, verify configurations, and restart apps without dispatching a technician.
6. Offline management. Kiosk devices in field service, logistics, and remote locations may operate without reliable connectivity. Standard MDM cannot push updates or commands to offline devices. Bento MDM’s Offline QR Commands close this gap — IT generates a QR code containing the policy update, a local worker scans it with the device, and the command executes without a network connection.
Bento MDM includes all 6 capabilities at $1/device. Kiosk mode is not an add-on, enterprise tier, or separately licensed feature. It is included with the same console and same per-device price as every other MDM capability — from enrollment through offline management.
Frequently Asked Questions
What is kiosk mode?
Kiosk mode is an MDM capability that locks a device to a single application or a curated set of applications. The home screen, settings menu, and navigation controls are disabled. The user interacts only with the approved app. When the app closes or crashes, the device automatically restarts it. Kiosk mode turns any enrolled device — tablet, phone, laptop, or ruggedized handheld — into a single-purpose tool for retail POS, patient check-in, digital signage, field service, or testing.
What is the difference between kiosk mode and Guided Access?
Kiosk mode (Single App Mode on iOS) is MDM-managed, persistent, and survives device restarts. It is centrally configured by IT and cannot be exited by the user. Guided Access is user-initiated, temporary, and requires a passcode to exit. Any user can enable Guided Access on any app at any time, and anyone with the passcode can disable it. For production kiosk deployments, Single App Mode via MDM is the correct approach because it is persistent, centrally managed, and tamper-resistant. Guided Access is suitable for short-term, ad-hoc single-app use — not for permanent kiosk installations.
Can I use kiosk mode on any Android tablet?
Kiosk mode (COSU) requires Android 6.0 or higher, and the device must be enrolled as a dedicated device with the MDM configured as Device Owner. This enrollment must occur during initial device setup — either via zero-touch enrollment or a QR code at first boot. A device that is already set up with a personal Google account cannot be converted to COSU without a factory reset. Most enterprise-grade Android tablets (Samsung, Zebra, Honeywell, Lenovo) support COSU. Consumer tablets running Android 6.0+ also support it, provided they are factory-reset and enrolled as dedicated devices.
How do I update a device that is in kiosk mode?
MDM pushes OS and app updates to kiosk devices over the air, just as it updates any enrolled device. Configure automated patching with an off-hours maintenance window so the device can restart for updates without interrupting its kiosk function. The kiosk app relaunches automatically after the update completes. If the device operates in a location without connectivity, Bento MDM’s Offline QR Commands can push the update via a locally scanned QR code.
What happens if the kiosk app crashes?
MDM configures kiosk mode with auto-restart — if the locked app crashes, the device automatically relaunches it within seconds. The user never sees the home screen or the settings menu. On Android COSU, the lock task policy ensures the app is pinned to the foreground and restarted on failure. On iOS Single App Mode, the supervised profile relaunches the app after a crash. If the crash is persistent (the app crashes repeatedly), MDM alerts IT through the monitoring dashboard so the issue can be diagnosed remotely.
Related Articles